What is ZT-NAC and why do you need it?
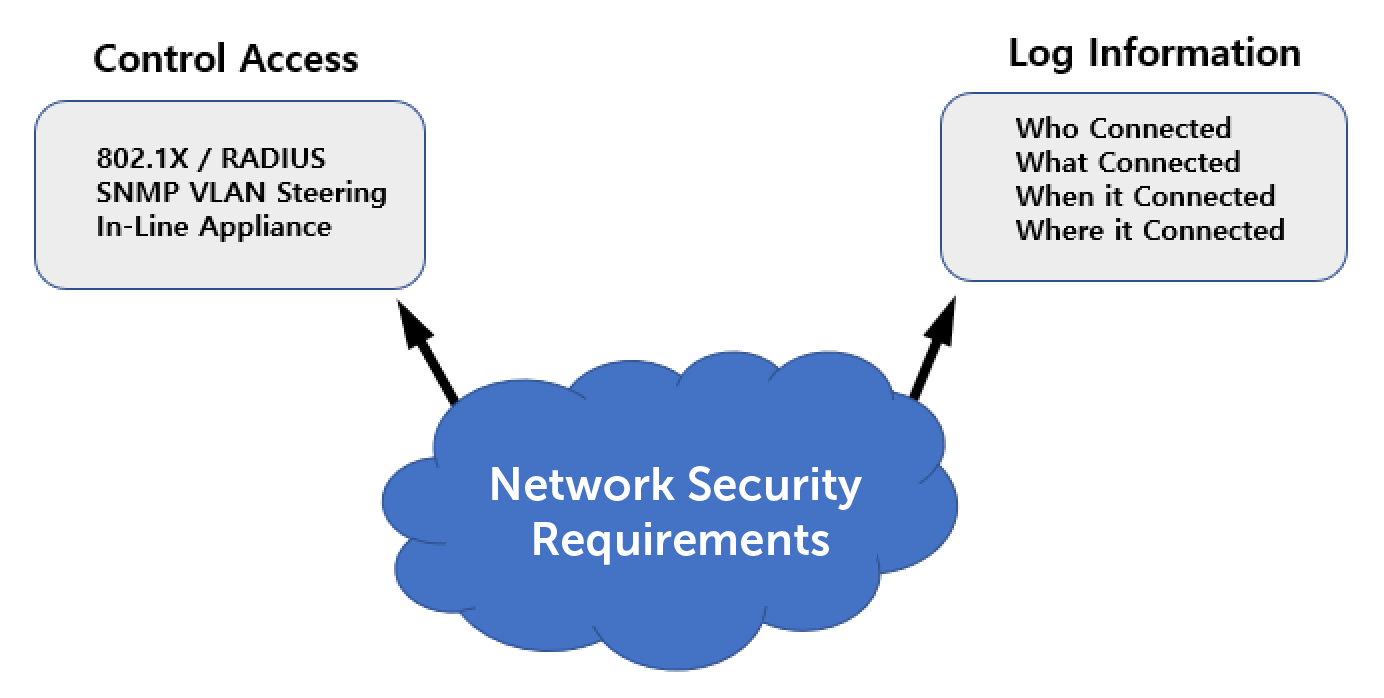
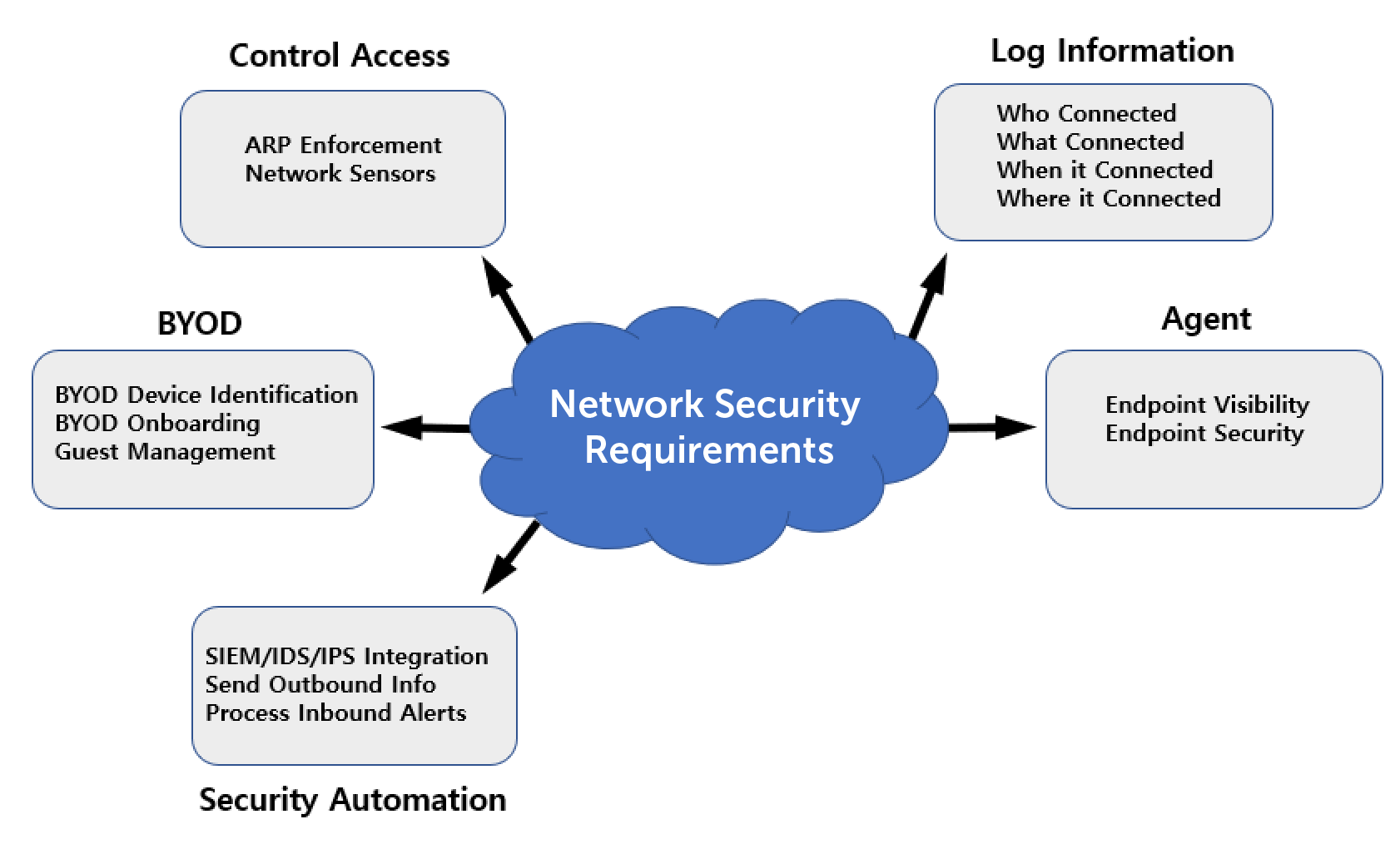
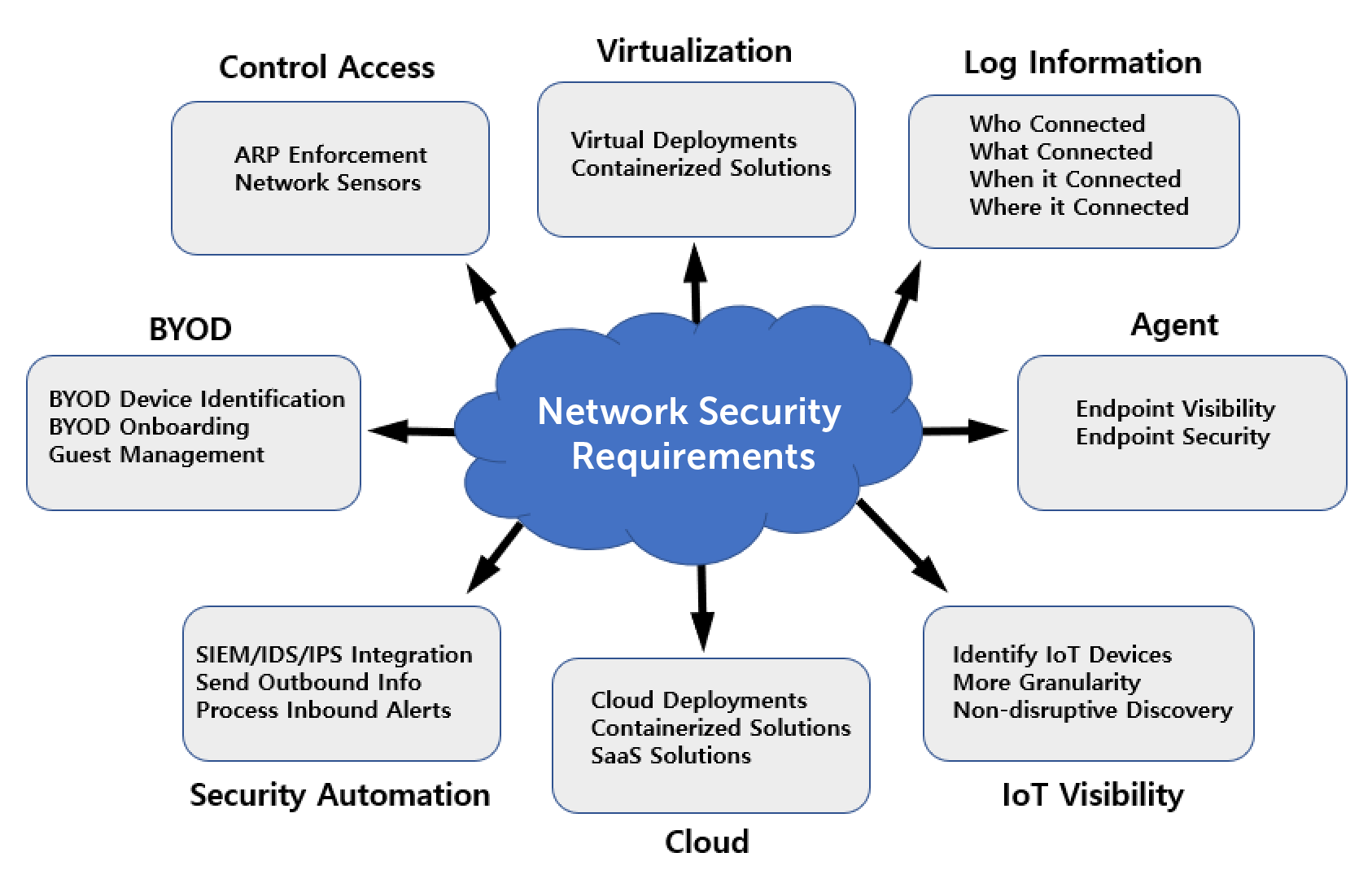
To answer this, let’s briefly revisit the evolution of Network Access Control (NAC). Over 15 years ago, NAC gained prominence in the market due to the recognition that internal access to on-premises corporate/organizational networks need to be restricted and information tracked regarding all network connections. The graphic below depicts some of the problems that earlier generations of NAC solved and how they were solved.
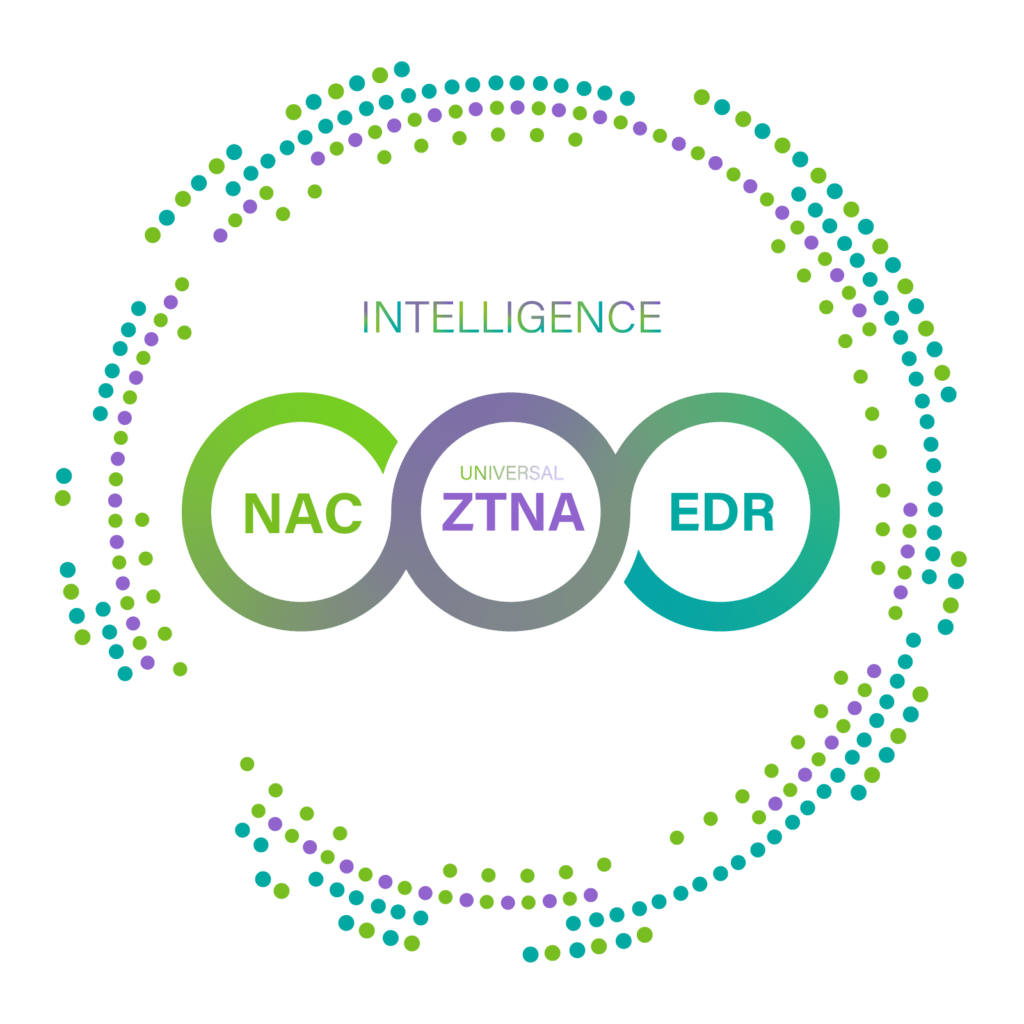
How does Genians ZT-NAC work?
Genian ZT-NAC incorporates all the traditional Genian NAC functionality combined with new features and capabilities to address today’s challenges. Just because the network boundary is now everywhere does not mean the building blocks of NAC are no longer required. Of course, you will want to know who, what, when, where and how but this must work in the new Digital Landscape which includes wired, wireless, Cloud, VDI, 5G and more.
Features and Components
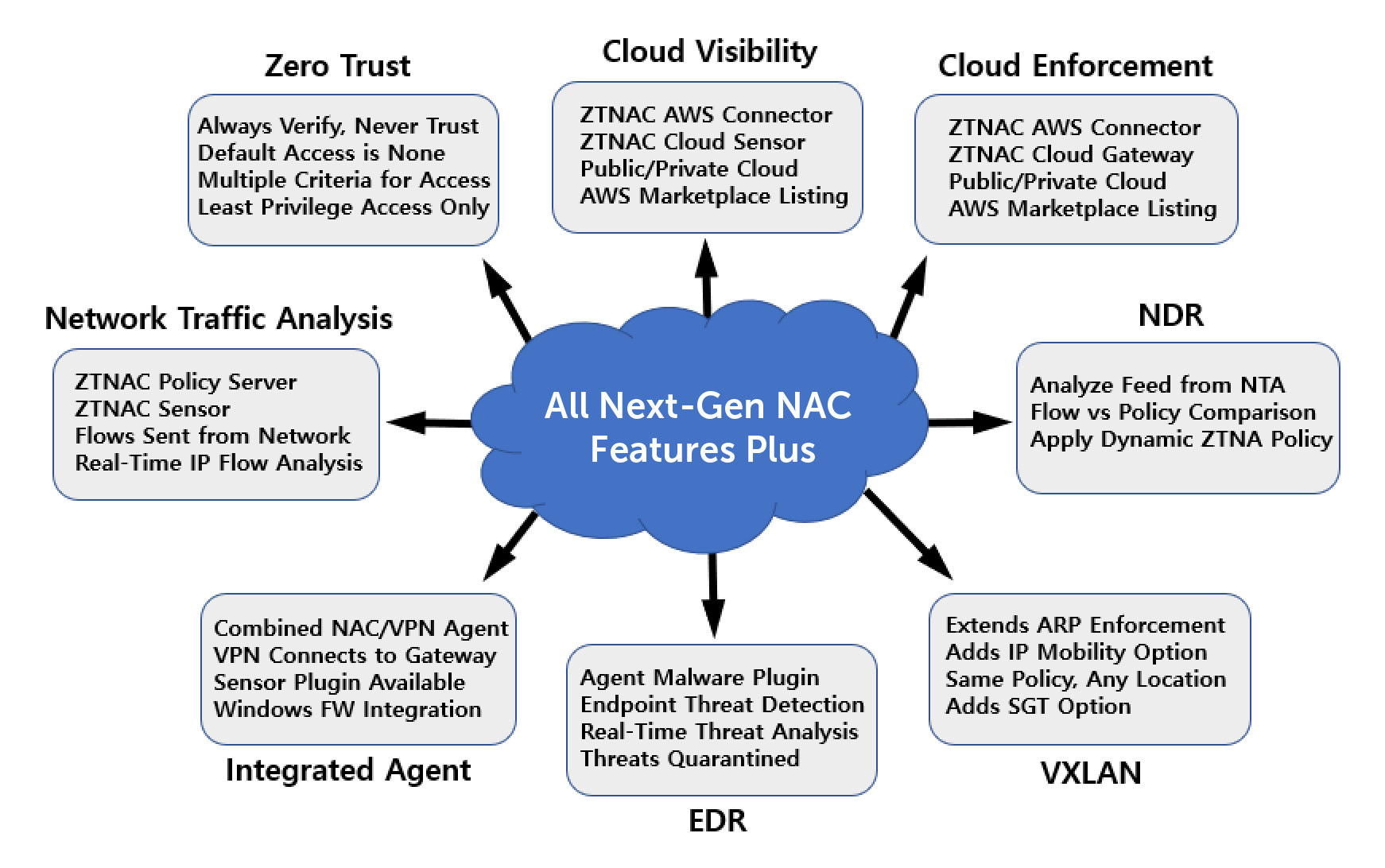
Below is a high-level overview of Genian ZT-NAC Features and Components. These features address the challenges of the new Digital Landscape to ensure your users, devices, and data are safe, compliant, and secure.
- ZT-NAC Policy and Component Management from a single UI: ZT-NAC Policy Servers are available in the Genians Cloud (SaaS), Public Cloud, Private Cloud or On-Prem and provide a single pane of glass for all ZTNA policies, components, users, devices, dashboards, reporting and integration settings.
- Visibility for ZT-NAC with Network Sensors: ZT-NAC Network Sensors can be deployed on physical Intel products, as VMs, Docker containers or Agents allowing for Public Cloud, Private Cloud, On-Prem, Branch or even Home applications. Providing Genian Device Platform Intelligence (GDPI), data collection as well as overlay and enforcement functions, Network Sensors are a key component of ZT-NAC.
- ZT-NAC Integrated NAC/VPN Agent: The ZT-NAC Agent provides full NAC Endpoint Security with over 50 available plugins, built-in client VPN functionality, Sensor functionality, and Access Control capability utilizing dynamic firewall rules on the endpoint itself.
- ZT-NAC Gateway: The ZT-NAC Gateway is available in Public Cloud, Private Cloud or On-Prem and may also be deployed as a Remote/Teleworker Gateway. It provides Authentication Services, Access Control to Internet and Cloud destinations, and is capable of applying dynamic QoS policies in real-time.
- ZT-NAC AWS Policy Connector: The ZT-NAC AWS Policy Connector allows for real-time command applications to EC2 instances in a monitored AWS environment. These commands are able to dynamically restrict what resources EC2 instances can access, completely quarantine an instance, or even shut an instance down. This provides a very granular level of control over instances in Cloud Native environments and ensures all EC2 instances are constantly in compliance with security policy.
- ZT-NAC Network Traffic Analysis (NTA): The ZT-NAC Policy Server processes and analyzes IP flow data from customer networks. Feeds are derived directly from customer routers/firewalls or from Network Sensors or Gateways. Collection of data is non-disruptive and provides critical insight into traffic patterns, volumes, applications, and destinations to enhance visibility for ZT-NAC.
- ZT-NAC Network Detection and Response (NDR): ZT-NAC Network Traffic Analysis is fed into the NDR Engine on the ZT-NAC Policy Server. The Policy Server compares network activity to configured ZT-NAC policies and performs an automated policy response based on violations.
- Network Virtualization Functions: Provides Network Overlay features allowing for ARP Enforcement over VXLAN, SGT policy enforcement and IP Mobility. IP Mobility helps facilitate standardization of ZT-NAC policies across an organization’s enterprise regardless of the location of the user or device. ZT-NAC policies can be persisted at HQ, Branch and even Home locations, drastically reducing the administrative overhead of implementing ZT-NAC.
- ZT-NAC Endpoint Detection and Response (EDR): Utilizing enhanced Agent plugins such as the Malware plugin, information is collected from endpoints for processing by the ZT-NAC Policy Server. Threat detection and response is managed by the Policy Server with various real-time enforcement actions applied (ARP Enforcement, Agent, Gateway). An enhanced Agent UI provides threat detection functionality that can be enabled and configured by end users to promote and encourage threat awareness within an organization’s population.
Genians ZT-NAC vs Other Solutions
As with traditional Genian NAC, Genian ZT-NAC gives customers a high level of control over the solution. With fully Managed Service ZTNA solutions, typical delivery is strictly on the solution provider’s platform/network and technology is bundled in such a way it resembles an “all or nothing” approach.
Fully Managed Service = Less Control and Customization
With Genian ZT-NAC, you control where you deploy various components on your network. Whether it be On-Prem or Cloud, many options are available. For example, for On-Prem components, ISO images or Docker containers may be installed on physical equipment or in virtual environments such as VMWare. Cloud components can be leveraged through the Genians Cloud (Managed) or deployed in your own Public or Private Cloud environment. This is especially valuable for Hybrid Cloud environments and allows customers to architect the solution that is right for their organization and topology.
Better Visibility = Better Security
Genian Device Platform Intelligence (GDPI) is also unique in that it provides more granularity into devices that goes far beyond traditional device fingerprinting. Providing images of devices, EOS/EOL information, correlated CVEs and business context, this level of visibility allows for more precise security policy enforcement. GDPI is also available as a separate product with a Cloud API, subscription model and even White Label options.
Simple Approach = Faster Deployment
Finally, ease of deployment and subscription billing models allow customers to start adopting a ZTNA approach in a shorter time frame than a traditional fully Managed Services approach, while keeping costs down and simplifying overall management of the project and product.