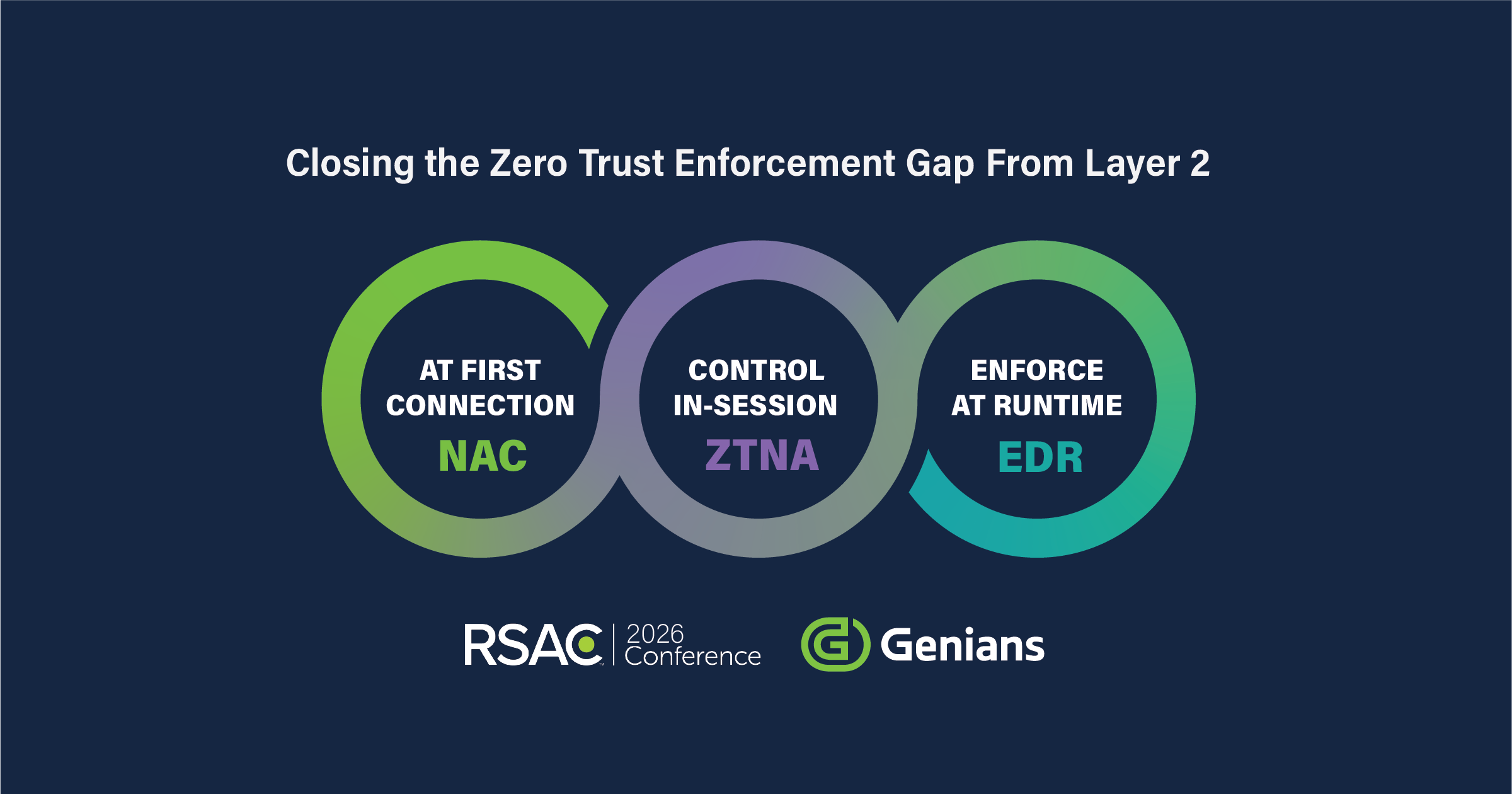
Compliance Velocity Begins at Execution
Policies matter only when they are enforced
Genians turns compliance requirements into execution. At the moment of connection, during every session, and at runtime, controls are enforced where decisions meet reality.
- Execution across connection, session, runtime
- Controls enforced at operational speed
- Evidence created at the moment of execution
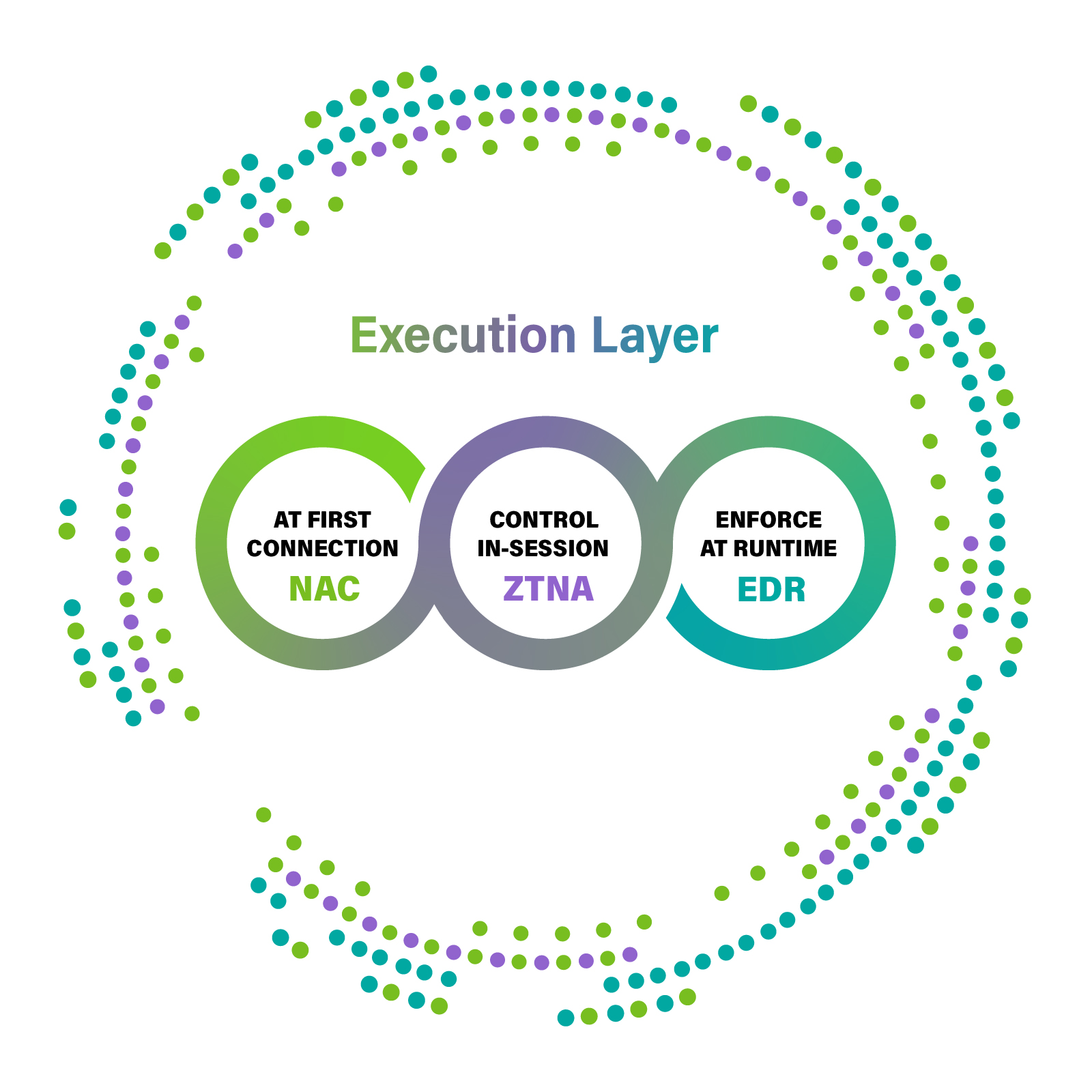
EXECUTION CONTINUITY
How Compliance Velocity Becomes Action
Compliance fails when enforcement resets between systems. Genians maintains execution continuity across connection, session, and runtime ensuring that policies remain active as access, context, and risk evolve.
What Makes Compliance Executable
- Device context available at the moment of connection
- Session control that adapts while access is active
- Runtime enforcement that responds instantly
- Shared execution context across NAC, ZTNA, and EDR
GENIANS
Proven at Operational Scale
Years
34
M
Over
100
K
Over
5000
Execution sustained across decades of change
Revenue built on long-term operational deployment
Active execution points across enterprise networks
Organizations running Genians in daily operations
TRUSTED IN REAL OPERATIONS
Trust Proven in Daily Operations




Running in production across 5,000+ organizations worldwide, from SMEs to Fortune 500s.
EXECUTION IN PRACTICE
Where Execution Meets Reality
FAQ
Clear Answers to Common Questions
Q. What do “Zero Network Changes” and “Zero Integration” mean when using Genians’ solutions?
Genians’ Network Sensing technology provides complete network visibility and access control without requiring changes to your existing network infrastructure or relying on integration with third-party systems such as Switches, Wireless Controllers, etc. This streamlined approach ensures effortless deployment and enhanced security.
Q. Genians offers NAC, ZTNA, and EDR solutions. Are they provided through a single platform?
No, each solution is available individually, but they can also be seamlessly integrated to work together, providing enhanced security and management capabilities.
Q. If I want to manage my Campus Network while using ZTNA, do I need to purchase NAC separately?
No, unlike other ZTNA solutions, Genian ZTNA already includes NAC functionality. By using Genian ZTNA, you can seamlessly manage Campus Networks, Remote Access, Applications, and Cloud security through a unified platform.
Q. How scalable are Genians’ solutions for various network environments, including legacy, hybrid, and evolving networks?
Genians’ solutions are highly scalable and designed to support all types of network environments. With flexible deployment options such as On-Premise, Cloud-Managed, and As-a-Service models, you can seamlessly expand and secure your network without disruption, regardless of its complexity.