Ensure Core Cybersecurity Requirements Are Met In This Unprecedented Time
Contactless Deployment Of Next-Gen Network Access Control
Quick Cloud Policy Server provisioning, Virtual Network Sensor installations, truly vendor-agnostic enforcement capability (based on ARP security), and low-complexity integration with 3rd party systems in the existing enterprise ecosystems, all allow for a low touch approach that can be fully implemented remotely.
The table below highlights some of Genians’ key features that make this possible.
Feature | Genian NAC provides |
|---|---|
Zero Trust & SASE Ready | • Non-intrusive network sensing and access control at the Edge • Policy-based network segmentation • Control traffic from any source to any destination, On-prem or Cloud • Various deployment options (Public, Private, Hybrid, or Multi Cloud) |
Device Platform Intelligence | Discover Devices’ business contextual (EOL, EOS, Manufacturer info) and risk-related (CVE) information along with their technical information (Device fingerprinting) without disturbing existing network infrastructure. |
Rapid Deployment | • Instantiate Policy Server in minutes by leveraging Cloud • No on-prem physical appliance installation required. • Install Network Sensor using VM or Agent |
Pragmatic Implementation | Start with free trial and upgrade anytime • Basic Edition for visibility • Professional Edition for access control • Enterprise Edition for automation |
Network Integration | • No changes required to existing IT security infrastructure • No Network device (Switch, Wireless Controller) updates needed |
IT Security Automation | Orchestrate a wide range of IT security solutions (Firewall, VPN, IDS/IPS, VM, MDM, SIEM, APT, DLP, CRM/ERP, etc.) to ensure unified policy enforcement. |
Working from Home (WFH) | • Illuminate all IP-enabled devices used by remote users • Granular access permissions by role • Optimized AAA services for remote users. • Unified control of BYOD, BYCD, and Guest management • On-going endpoint compliance check |
Genian NAC Enhancement with customers
Genian NAC is always evolving, adapting and improving. With over 1,600 customers of all sizes and in all verticals utilizing the product around the world, each one plays a key role in shaping the capabilities of our solution. Their wide-ranging requirements ensure a steady stream of feedback representing every use case imaginable – a broad set of perspectives that Genians leverages to build an even more powerful and successful product.
For example, a global manufacturer with an enterprise network spanning multiple countries, several hundred thousand endpoints, and a heavy focus on IoT/OT will certainly have a different set of use cases and requirements than a small municipality or school district. Genians’ attention to enterprises’ changing needs ensures we have a product that can satisfy customers with vastly different requirements in terms of scale, functionality, network architecture, performance, and specific business needs.
The pie chart above represents the new features and product improvements made during 2020. The story these numbers tell is clear:
- Functionality: Clearly customer demand for products to simply “do more” is the top priority. This is not unique to Genian NAC. With most organizations consolidating security solutions from dozens of existing systems, the more a single product can do the better.
- User Interface and Experience: Added functionality must not come at the cost of complexity. Ensuring that both the web interface and experience for users is clear and easy to understand is critical.
- Agent: With traditional approaches to security falling short, endpoint visibility is becoming more critical. Having visibility into the applications installed and running, exposing vulnerabilities, monitoring events, and tracking open ports on an endpoint are just some examples, but capabilities must continue to be enhanced for Agents. Also, customers are consolidating agents as they understand now more than ever how agents themselves can pose a security risk.
- Logging: Why so many improvements on something as seemingly basic as logging? Simply put, logs are the portal into what is happening: on the endpoint, in the network, with a user or a device. Filtering and harnessing log events is key to facilitating Security Automation which helps automate the process of securing your environment. More security, less manual work.
Genians in 2021
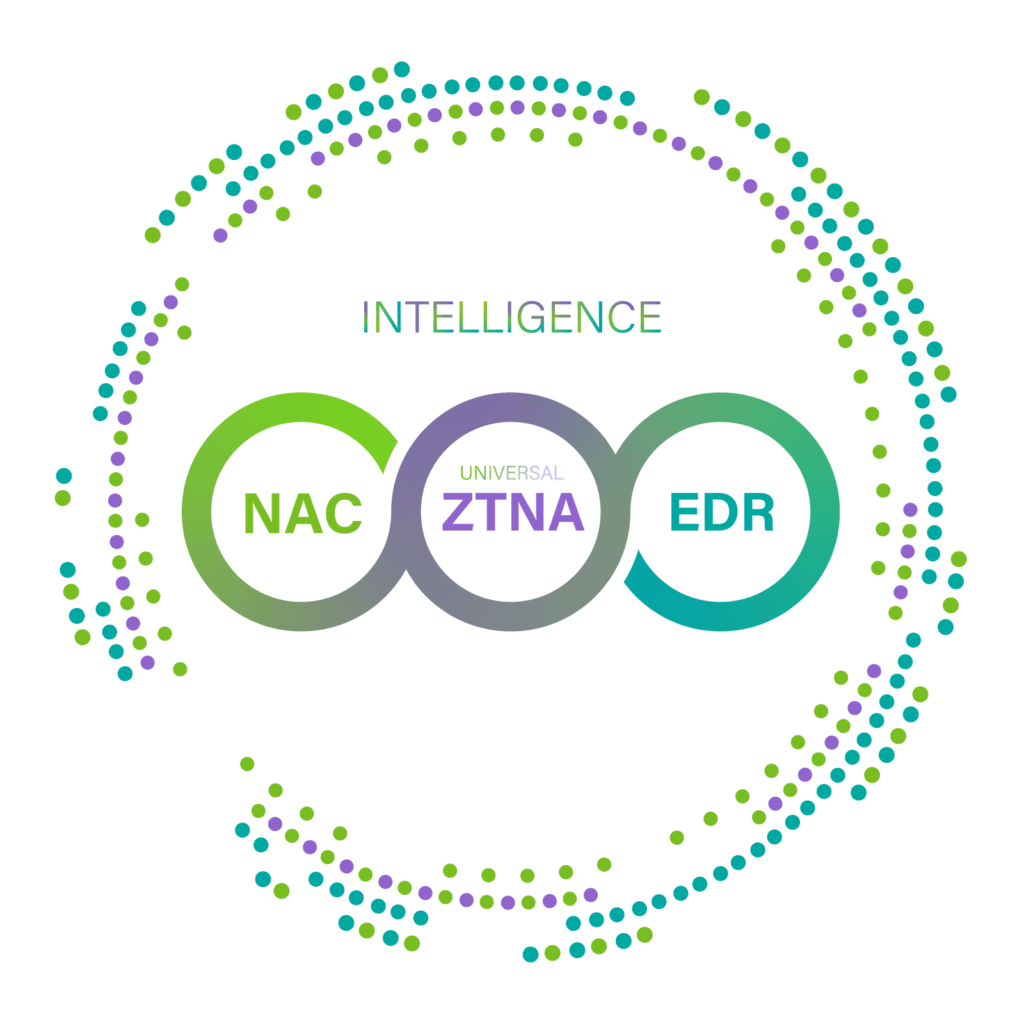
Genians will continue to deliver a comprehensive cybersecurity platform to secure the Edge in the most efficient way. Genians’ platform provides any organization with the most essential cybersecurity features and functionalities by delivering Device Platform Intelligence (DPI), Network Access Control (NAC), and Endpoint Detection and Response (EDR). 2021 will be the pivotal year to blend all together. Also, these act as seeds from which one can cultivate a robust cybersecurity environment for better digital trust.

Zero Trust & SASE Ready
Genian NAC
With major structural changes and enhanced focus on Zero Trust, Genian NAC will continue to provide all of the capabilities our customers have grown to appreciate and are presently utilizing. However, security must be provided regardless of where a user connects and where the application resides. Controlling access to on-prem resources, Internet and cloud applications for any user in any location and then adapting the access in real-time based on identity, status and conditions are among new features to expect. If this is beginning to sound like SASE, that is not a coincidence. Stay tuned. A major release will be coming this year.
Next-Gen Device Fingerprinting
Genian Device Platform Intelligence
It will continue to play the critical role it does today as the foundation of non-intrusive visibility for Genian NAC. Due to high demand from customers and partners in 2020, GDPI has continued to evolve into separate usages for those such as MSPs highly focused on NAC as a Service. Take simple 3 steps to enhance network visibility and empower your MSP’s cybersecurity business by leveraging GDPI.
The Best Practice of GDPI
- Comprehensive Device Fingerprinting
- Specific Platform Assigned
- Assign Groups or Permissions
The Usage of GDPI via Cloud API
- Expose API
- Enable Free Tier
- Solicit Feedback from Partners / MSPs
Empower MSPs with GDPI
- Productize
- Enable Paid Tier
- MSPs choose Tier, DB, and Branding
Enhanced EDR Solution empowered by NAC
Genian Insights E
Endpoint Detection and Response will see its introduction into the Global Market. With a dominant position in the South Korean domestic market, Genian Insights E is seeing explosive growth with the high demand for EDR. EDR picks up where traditional endpoint security agents reach their functional limit. Continuous in-depth monitoring, machine learning (ML), X behavior analysis (XBA), automated incident response and visualization with dashboards are all features of GIE.