Network-connected end devices remain a major cybersecurity point of vulnerability. Network Access Control (NAC) technology provides the ability to lock down network access in a way and to an extent that no other cyber defense product category does. Cyber threats in today’s enterprises are focused on multiple attack surfaces across the entire range of network-connected devices. Over the past few years, the number of endpoint attack surfaces has expanded considerably. This trend is expected to continue and increase exponentially in the years immediately ahead.
Endpoint attack surfaces are expanding in terms of client platform diversity, and include:
- “Traditional” stationary desktop devices
- once the majority
- now increasingly in the minority of device types
- The explosion of mobile device types and numbers, from laptops to tablets to smartphones
- Employee, contractor, and vendor-owned “BYOD” (Bring Your Own Device) equipment requiring network access
- Exponentially increasing numbers of “IoT” (Internet of Things) devices that require network connectivity (wired and wireless)
And also in terms of platform depth:
- Multiple operating system platforms (Windows, OSX, iOS, Android, Linux) and versions
- Multiple application and database platforms (OpenStack and proprietary)
- Multiple storage technologies (SAN, NAS, DAS, Cloud)
- Both wired and wireless connections
- Multiple device configurations
Each specific device and platform provides its own unique set of attack surface vulnerabilities. All need to be actively managed from a network connection perspective to ensure they aren’t a threat to the enterprise environment. This requires ensuring all devices can be accurately identified, that all have been appropriately patched and updated to ensure O/S and application-level vulnerabilities have been remediated, and that devices are operating with the latest anti-malware/anti-virus software definitions prior to gaining network access.
Current cybersecurity trends
- Cybersecurity best practices have long dictated an active device management approach. Many tools exist to accomplish this, but the ongoing network breaches, data exfiltration, and business outages experienced in recent years indicate that endpoint device management continues to be a point of significant vulnerability in enterprise and organizational environments small and large
- Ransomware, focused on exploiting vulnerabilities at the network client endpoint, rose quickly between 2013 and 2016 and now sits at ~$1B in ransom payments annually
- Email phishing exploits remain even more profitable at $1.7B annually over the past 3 years
- Both ransomware and email exploits focus on the endpoint
- Further, the number of IoT devices is expected to increase exponentially in coming years (a process already well underway), with the number of enterprise network connections soaring accordingly
- The network traffic generated by IoT devices will be unlike anything yet experienced (25 billion devices expected by 2021 from 10 billion today), and will not be possible to manage via manual means (ie responding as needed to all alerts, scanning traffic in real-time or in logs). Automated and “prescribed-in-advance” policy-based security management will be required. NAC solutions provide that capability.
- The cost of cyber-defense continues to climb higher, and is expected to continue to do so. We don’t even really know how much current cybercrime activity costs us, but a recent, conservative Wall St. Journal estimate puts it at $2T annually in 2017 (other estimates range from $3-$6T, with the higher end of that range expected to be reached by 2021)
- In terms of how much enterprise IT spends on cybersecurity defense products annually, it is estimated that the global cybersecurity spend was $75B in 2015; that is expected to increase to $100B by 2017 YE; and further to $200B by 2020
In short, attack surfaces are expanding quickly, breaches continue to be a major problem, cybersecurity costs are clearly out of control, and the ability of enterprises to successfully manage these challenges continues to fall short – often in the simplest of ways. Indeed, most major breaches turn out to be the result of operational shortfalls in the area of updating and patching operating systems and various application components. Beyond that: Cisco estimates that even when IT departments are alerted to a potential problem via monitoring and alerting, only 56% of active alerts are actually responded to.
Clearly, effective operational management of network-connected devices from a cybersecurity perspective in any organization requires a rigorous and disciplined alignment of the correct tools, technologies, people, and processes. NAC technology provides the key, foundational component necessary for enterprises building a modern, effective cyber-defense framework.
NAC As a Key Component of Your Cyber Defense Framework
At our current juncture, with cyber assaults already outstripping enterprises’ ability to respond effectively, there is obviously a pressing need to reevaluate cyber defense strategies. For NAC vendors, a very large opportunity exists for making the case for increased NAC adoption. As the total market value for the sector (~$685M in 2017) is expected to approach $1B in the next 3-4 years, it isn’t a question of whether this market will continue to grow but by how much and how quickly. That said, the lion’s share of press on cyber-defense and cyber thought leadership is currently focused on seemingly newer, higher-profile cyber-defense innovations such as SIEM and ML-AI based predictive analytics rather than on network access control. Yet it is increasingly recognized that there is no “one size fits all” answer to constructing an effective cybersecurity defense framework. The market trend is therefore in the direction of integrating tools from across the cybersecurity product spectrum in a way that provides the best solutions for a given enterprise. Given its foundational role in providing for secure network access, NAC needs to be at the forefront of any network cyber defense architecture.
Legacy strategies and tools must be integrated into this new multi-layered cyber defense approach as well. Traditional firewalls, once the primary, if not the only, tool in the security toolkit, are now recognized as inadequate in and of themselves to provide the necessary defensive bulwark. This is because, as with many security approaches, they address just one aspect of the challenge – in this case protecting the network perimeter. However, if ever breached, whether through brute force attack or simple misconfiguration by a network administrator, perimeter security alone cannot prevent an attack from spreading laterally once inside the network itself. Likewise, with simple endpoint security: the moment the endpoint is compromised, all devices connected to the same network become potentially highly vulnerable as well.
So while it is widely recognized that a multi-layered, integrated approach needs to be taken to ensure effective cyber-defense, the cybersecurity products marketplace has become glutted with a plethora of competing products, platforms, and contradictory claims. Genians has an opportunity to assist prospective customers by clarifying the key security ingredients that matter most in what has become a very confusing marketplace. For example:
- The emergence of “SDP,” or “Software-Defined Perimeter” as an alternative to NAC. This is misleading as it simply “moves the boundary” by redefining it. Whether software-based, or hardware-oriented, as in the case of traditional firewalls (which is really a combination of hardware and software), perimeter security alone is problematic. There is always the danger of perimeter penetration. SDP is also very new technology, untested in the market, and thus at this point very much an unknown quantity
- CASB, or Cloud-Access Security Brokers, provide security between cloud customers and providers. Features and functionality will vary from one cloud provider to the next, so customers will have to take care to understand what their particular CASB/cloud provider security offering will amount to. Again, security needs to be approached as a complex, multi-faceted challenge, not something that can be addressed with a single solution. In no way should these cloud broker solutions be considered fully-comprehensive defensive frameworks
Summary
Cloud computing brings with it both great flexibility and significantly increased infrastructure complexity. For most enterprises, it is important to keep in mind that “the cloud” will not be a single, monolithic entity, but rather a combined physical/virtual infrastructure platform that will include both on-premise and off-premise components. Indeed, it will very likely include more than one cloud provider. Hence the terms “hybrid” and “multi-cloud” environments.
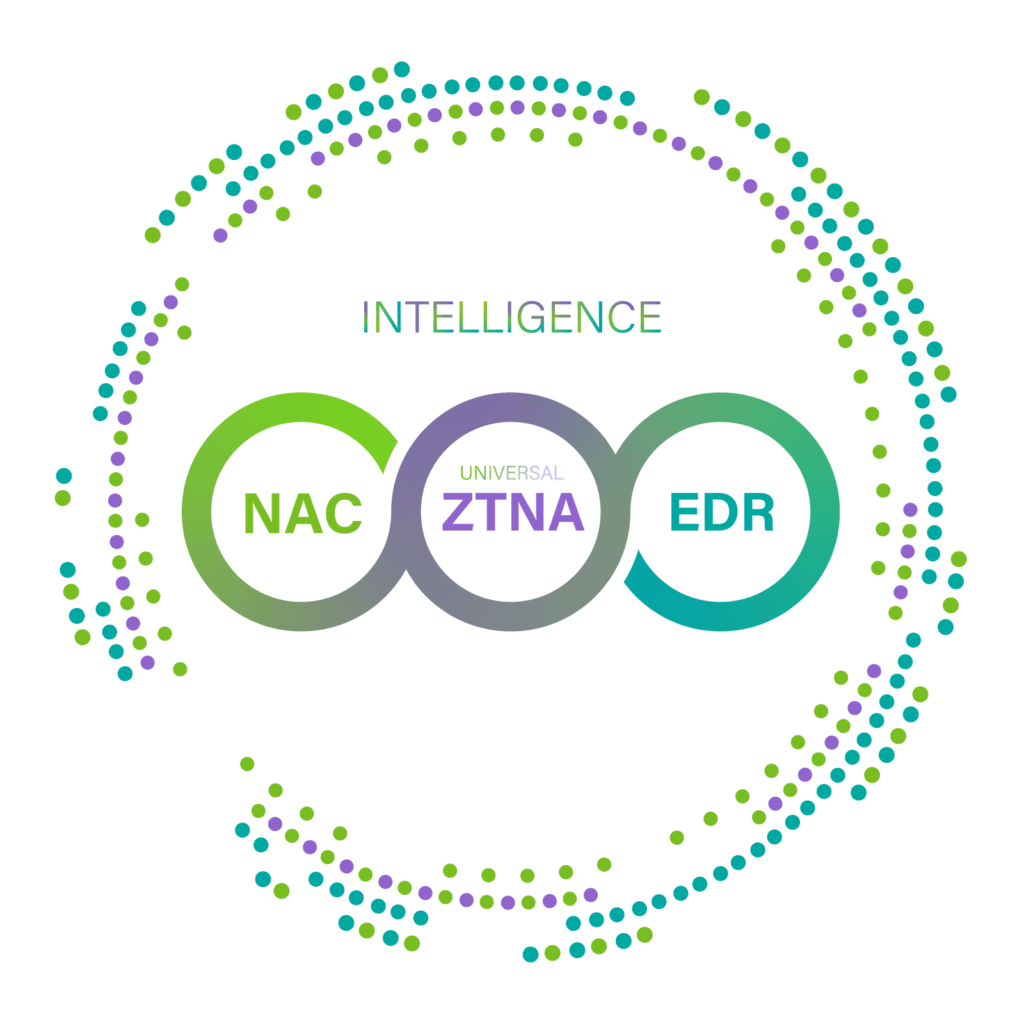
Security solutions will need to effectively address this new complexity. NAC, SIEM, and ML/AI-based predictive analytics tools should therefore ideally be employed together in a joint, comprehensive cyber defense solution. NAC can play a primary, critical role in this integrated framework by being leveraged as a conductor to orchestrate all meaningful information emanating from SIEM, analytics, and other security tools to ensure action is taken at the right time and in the right way to mitigate cyber threats to your network.
In summary, enterprises need to:
- Reevaluate their Cyber Defense Strategy
- Understand there is No “One Size Fits All” Solution
- The Best Approach to “Defense-in-Depth” is Multi-Layered and Integrated
- Beware of Untried Approaches – “The Shiny New Objects”
- Establish NAC as the Center and Foundation of your Security Framework – Your Cyber Defense Conductor