It’s rare that situations that involve the IT community at large break through into mainstream consciousness. If you are a CIO, business owner, or network manager, every day brings challenges related to the integrity and security of your network. The general public doesn’t usually hear about what happens every day in the world of IT. But, when something major happens, it’s all anyone can talk about. That’s what happened on May 12th and as of this writing is still occurring in various capacities.
Suddenly, the whole world is talking about something called WannaCry.
WannaCry is what is known as ransomware. Ransomware is not a new threat. It has already cost businesses all over the world billions of dollars. If you manage a small to medium-sized business, you are well aware of the threat. It’s estimated that ransomware costs businesses in the small to medium range about $75 billion annually. So, why the media hysteria over this latest ransomware attack?
What makes WannaCry different?
WannaCry has been a different experience. This is really the first major attack to hit globally nearly all at the same time. At its peak, it was affecting firms in about 70 countries simultaneously. The biggest target, and possibly the reason why it got so much attention, was the National Health Service in the United Kingdom. When this happened, the stakes became very real for the general public. Business owners are used to breach attempts in an effort to steal financial information. The general public, however, is bound to respond to a cyber attack that actually puts people’s lives at risk. Horror stories about being unable to access information or do much of anything while people were in the hospital for treatment confirmed our worst fears. Now more than ever, business owners are scrambling to shore up their networks to defend themselves against the next attack. But, what should they know about their vulnerabilities?
Updates, the IoT, and surveillance
Large scale ransomware attacks like WannaCry are just one part of the equation. One specific type of attack shouldn’t be the focus when looking for a network security solution. That’s what makes a solution like a Cloud-based NAC the ideal monitoring and security solution for the modern organization. If a brief summary or overview could be given of what the most pressing information security matter is right now, it would be the proliferation of unknown devices currently accessing or attempting to access an organization’s network at any given moment. It could be anything from full Windows desktops down to smart devices that make up the Internet of Things. The IoT is especially worrisome because smart devices often have the lowest security measures built into them. It’s for this reason that they are often exploited and used to launch large-scale attacks. Even worse, visibility of them is often low.
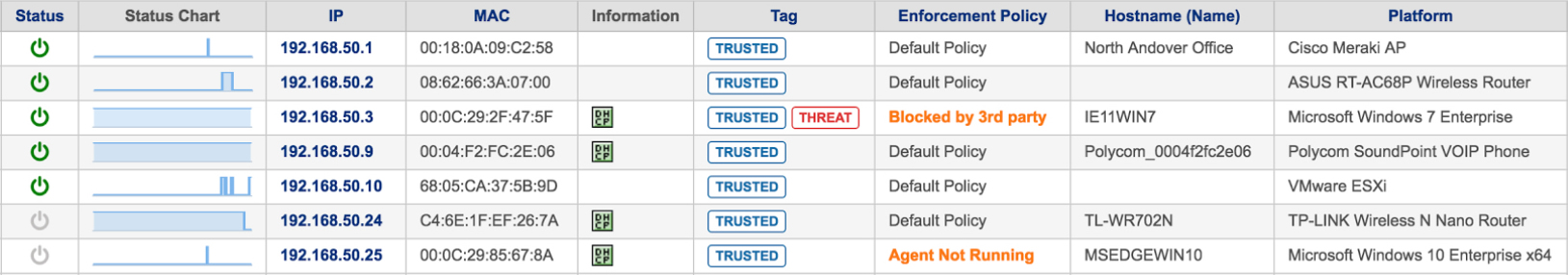
Device platform information is a vital element in the world of IoT
 The IoT has significantly complicated network security because in many cases, IT administrators are not even aware of what those “things” are, what they are doing, who is using them, and how they are being used on your network. A key detail to keep in mind is that the most effective network security solution will be able to provide you with all the information about a device you need to know, down to the platform running on that device.
The IoT has significantly complicated network security because in many cases, IT administrators are not even aware of what those “things” are, what they are doing, who is using them, and how they are being used on your network. A key detail to keep in mind is that the most effective network security solution will be able to provide you with all the information about a device you need to know, down to the platform running on that device.
To circle back to WannaCry for a moment, the reason why it was able to spread so far so quickly was because it exploited out of date software. Many of the attacks could have been stopped if the organizations’ Windows installations were actually properly patched and updated. That’s why we saw Microsoft release unprecedented security patches for abandoned platforms like Windows XP.
The modern firm needs a network security solution that can monitor all devices accessing the network as well as identify when those devices need to install a new security patch. Genian NAC can provide that information and more.
Genian NAC provides the most accurate device platform information
Genian NAC doesn’t provide you with some of the information you need. It provides you with the most accurate device platform information without using Agent. Take the example above. “Windows” while somewhat helpful as far as identifying what a device might be isn’t really as useful as it could be. Being able to see the actual OS release name helps better account for what is accessing your network.
There is a tremendous difference between a device running Windows 10 having access to your network and a device running Windows XP. While both can present security issues, it’s the older, outdated system that carries higher risks. Genian NAC can detect them all and control them in most efficient ways.