Ask any kind of IT professional what their greatest challenge is and they will probably answer with “uncertainty.” Uncertainty can be caused by many things. The impossibility of predicting employee behavior is one of these causes. Often, the biggest security vulnerabilities are caused by someone inside the firm who meant well but implemented a solution without understanding the risks involved. Uncertainty is closely tied with visibility. Not being able to see a problem when it first occurs can lead to major organizational security vulnerabilities.
Rogue APs Are A Serious Problem
A common example of damage caused by employee mistakes and administrative uncertainty are rogue access points, or “rogue APs”. Rogue APs often go undetected until a security breach occurs via that device. Typically, this device is a simple, cheap router that was improperly installed into a network without alerting anyone in management about it. Typically, an employee installed with positive intent to extend a wireless signal or to help other employees in the area connect their personal devices to the network wirelessly. However, a rogue AP isn’t always the product of a well-meaning employee. It can also be installed by a malicious actor with the knowledge that this router could be an access point at a later date. Regardless of intent, the security risk is the same.
Here’s how a typical scenario plays out. An employee brings their own router in and connects an ethernet cable so that it can access the network. The router is not actually configured in any kind of meaningful way, because it has been configured without the guidance of skilled IT staff. Access to the router, and therefore the larger network has either weak security measures or none at all. As long as this AP provides a reliable network connection, users may never alert IT staff of its presence, and this glaring security vulnerability goes undetected until it is exploited. Now you have an attack on your hands from a seemingly unknown origin. All of this has happened because the rogue AP wasn’t detected at the time it was installed.
Early Detection Is Key to combating Rouge Wireless devices
In the typical office setting, there are dozens of devices connected to a network. Everything from employee laptops to smartphones, even rogue APs. Unless you’ve installed every piece of WiFi equipment yourself and constantly walk around to physically take inventory of it, it’s nearly impossible to tell if a router is actually a rogue access point. Rogue APs must be discovered through a detection workflow. Software will need to be leveraged to find this unauthorized router.
Establishing the right kinds of protocols to properly identify rogue APs and save time doing so can be difficult. Additionally, IT managers have to decide just how much software they are willing to invest in order to meet their security needs. All these challenges can be solved easily through Genian NAC.
Smart Visibility To Control Rogue APs
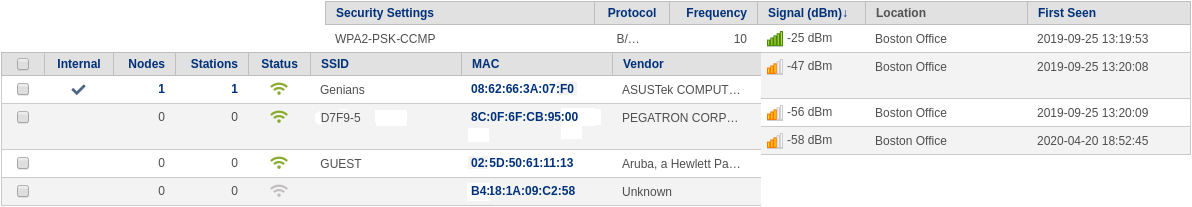
Genian NAC can detect wireless signals in your environment and determine which are originating from within your networks. With this visibility, you can easily detect, locate, and block rogue AP’s, or devices connecting to them, while providing instant alerts to administrators.
Three Simple Steps to Block Rogue AP’s
- Identification (Friend or Foe): Create WLAN groups for your approved SSID’s , and unapproved internal SSIDs (Rogue SSIDs)
- Classification: Create a node group for rogue SSID devices and set “SSID / is one of / [Rogue SSID WLAN Group]” as a membership condition, or add the membership condition to an existing group for devices to be blocked.
- Action: Link the group to a new or existing enforcement policy and configure permissions, or other enforcement options.
These simple three steps will lockdown any types of Rogue APs out of your network without disturbing existing wireless infrastructure. To further enhance security response, outbound messages can also be sent to an IPS, firewall, SIEM, or other solution.