The Hidden Headache: Duplicate IPs on Your Network
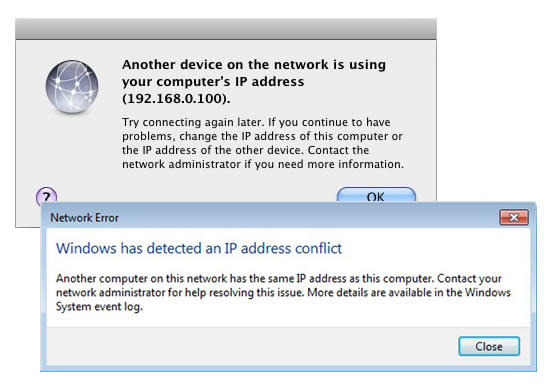
If you manage a network, you know that sometimes things don’t always go smoothly when it comes to identifying devices. One such difficult, and somewhat common, scenario is needing to manage duplicate IP addresses. An IP conflict can happen for a variety of reasons. When it does, it can cause issues regarding worker productivity by keeping devices offline. While the causes of a duplicate IP address that leads to conflict are rarely malicious, sometimes it can be cause for alarm if there is also an unauthorized DHCP server involved.
Why DHCP Doesn’t Always Play Nice
 Generally, though two devices sharing the same IP and being unable to access the network is a matter of a “glitch” with your DHCP. This can happen because of the way static and dynamic IP addressing is handled. It is rare to have static IP addresses for things beyond a company website, email, or other highly specialized use cases. It would be impractical and expensive to give a static IP to every device on your network. That leaves the DHCP to dynamically generate and assign IP addresses to devices as they connect to the network.
Generally, though two devices sharing the same IP and being unable to access the network is a matter of a “glitch” with your DHCP. This can happen because of the way static and dynamic IP addressing is handled. It is rare to have static IP addresses for things beyond a company website, email, or other highly specialized use cases. It would be impractical and expensive to give a static IP to every device on your network. That leaves the DHCP to dynamically generate and assign IP addresses to devices as they connect to the network.
Where the conflict can arise is when a wireless device is out of use for a period of time, usually in sleep mode, and its IP address gets reassigned to a new device. Laptops often behave this way. After going to sleep, the laptop will wake up and try to connect to the previously used IP address that has already been reassigned to another device on the network. An additional complication can be the introduction of smartphones and tablets to the network. iOS devices in particular have a tendency to try and maintain the same IP address after first connection with a network. If that device leaves the network for the day and then returns the next, it may try to force that original IP address when it is now in use by someone else’s laptop, yielding an error.
Resolving IP Chaos with Visibility and Control
Assuming that there is nothing malicious going on, the issue at hand is getting your people back online quickly by identifying why devices are now using the same IP and being blocked from accessing the internet. This is easier said than done.
In case you manage IP statically or dynamically using DHCP, it will be the challenge to:
- Detect/resolve/prevent IP conflicts
- Detect unauthorized DHCP server
- Manage authorized IP addresses for certain devices/groups
- Manage MAC and IP-based user authentication
- Assign IP address for networking devices (e.g. Router/Switch/Access Point Ports)
- Track down the history of changes on IP/MAC usage in real-time.
Without the proper tools to quickly identify and manage every device on your network, you’ll waste precious time going through all the IP addresses and devices. Genian NAC can help you quickly detect and resolve IP conflicts along with many other network related issues.
Genian NAC approach
Genian NAC can provide an all-in-one solution which includes IPAM, Built-in DHCP Server, and NAC (without Agent) and provides the most intuitive interface to manage IP addresses more effectively.
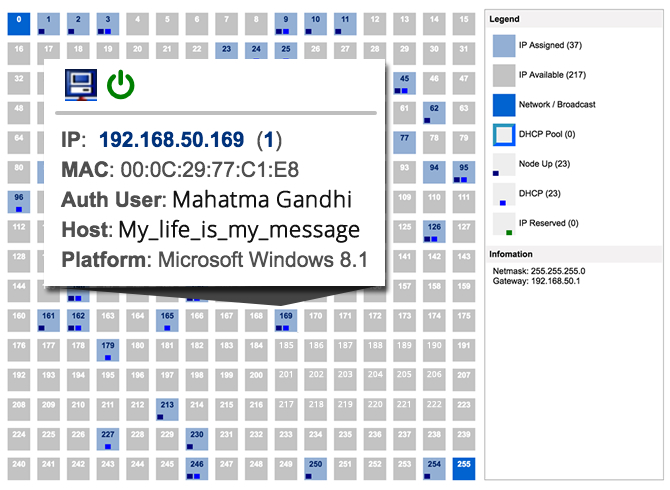
Smart Visibility of IP Address
While various types of devices are discovered, IP associated with the device is also detected by Genian NAC. Through intuitive IP matrix interface (Class C Subnet mask), you can easily find out how many IP addresses are being used and available, IP assigned by DHCP, reserved IP, and more.
Control IP Address
Provisioning IP addresses are critical to managing all types of devices more efficiently. So, Genian NAC can help you to plan, monitor, and control IP address usage dynamically and securely.
- Force devices/ports to use only specific IPs
- Change an incoming IP address to another IP
- Resolve and Prevent IP conflicts
- Reserve IP addresses (If a non-authorized user tries to use that reserved IP to access the network, the access is denied.)
- Apply Node policy to IP address instantly.
Most importantly, Genian NAC can assign IP addresses to only compliant devices right-on-time, and all historical access logs of IPs should be saved to support regulatory compliance.