In a recent blog post, Ripple20 – Detect and Isolate Vulnerable Devices at Risk, we discussed the background and effects of Ripple20 along with a mitigation approach using Genian NAC to identify vulnerable devices on the network by Platform type. Using affected Cisco devices as an example, we demonstrated how to quickly and easily identify vulnerable devices on the network. Today, we will cover how to identify the devices by CVE correlation.
The goal will be similar to the goal defined in the last blog. Identify vulnerable devices, group them together, restrict or modify permissions (if desired) and automatically notify Admins. The difference is we will be grouping them by CVE, not by Platform type. Let’s start with the first step – Identify.
Step 1: Identify Nodes by CVE
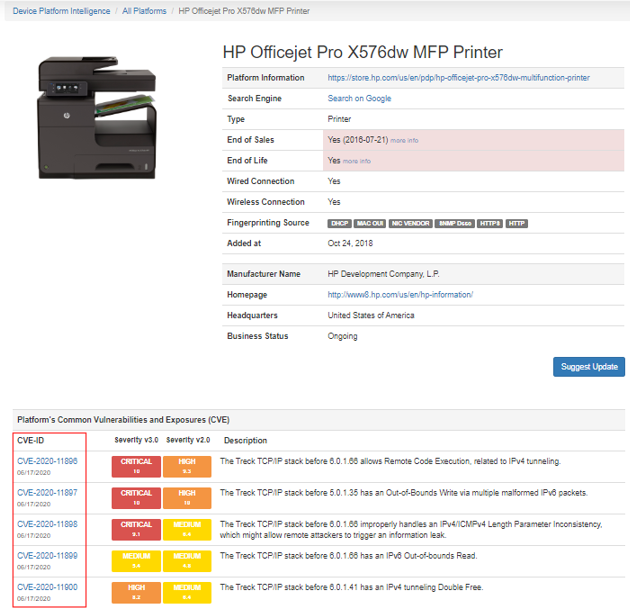
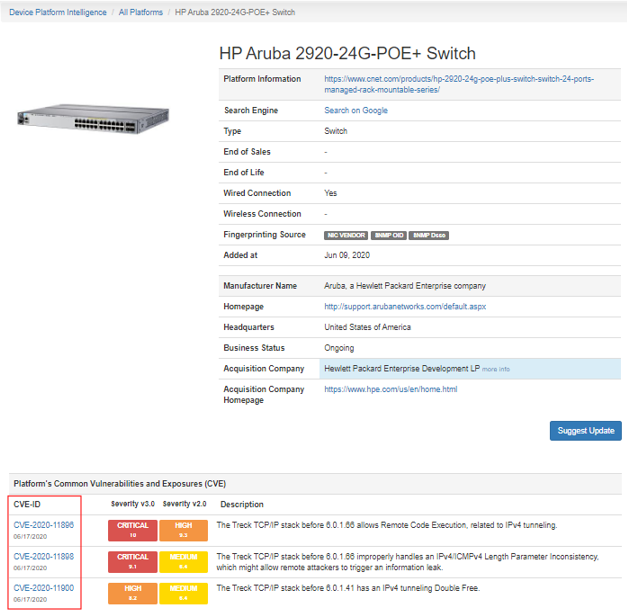
Leveraging Genians Device Platform Intelligence, a Genian NAC Sensor can be deployed on the network rapidly to non-intrusively identify all IP-enabled devices on a network. Sensors can be deployed as intel-based hardware, virtual instances or even utilizing the recently added Windows Sensor Agent Plugin which allows a Windows machine to act as a Sensor. Whichever method is chosen, it will quickly identify all devices on the network and display them in the UI.
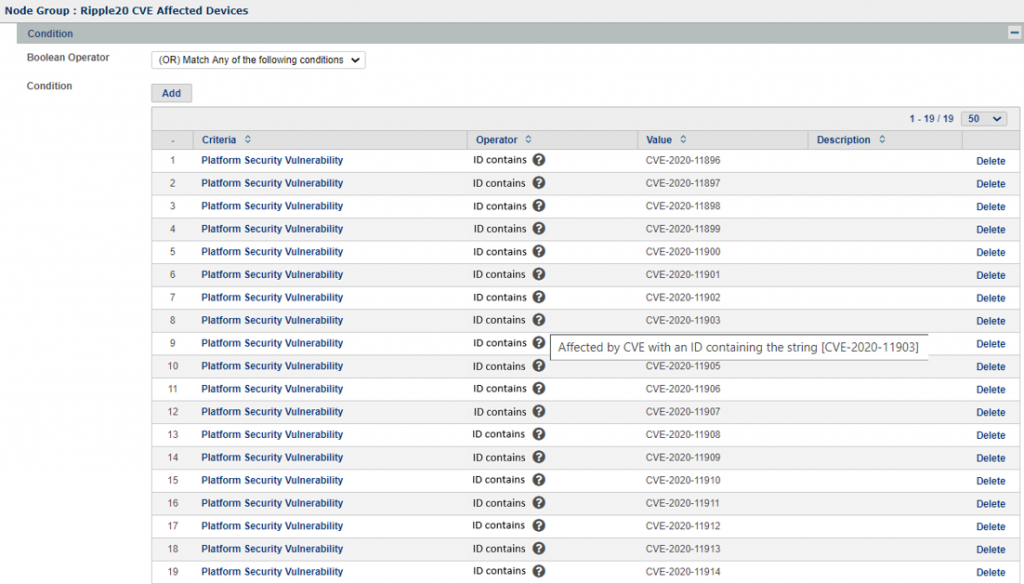
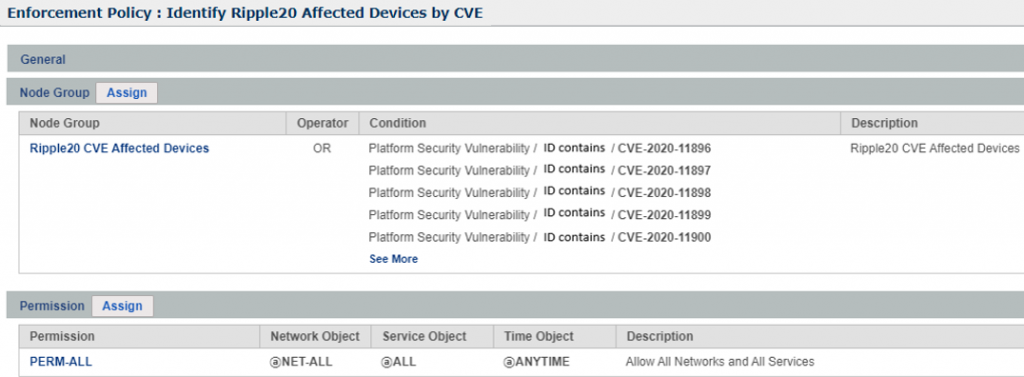
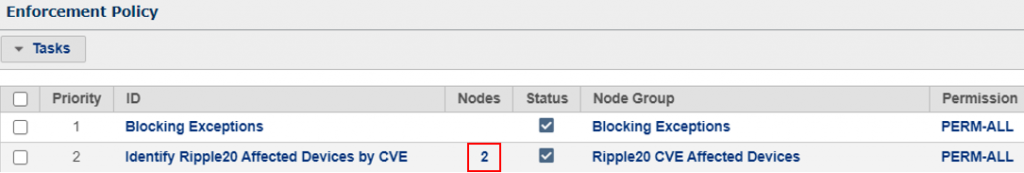
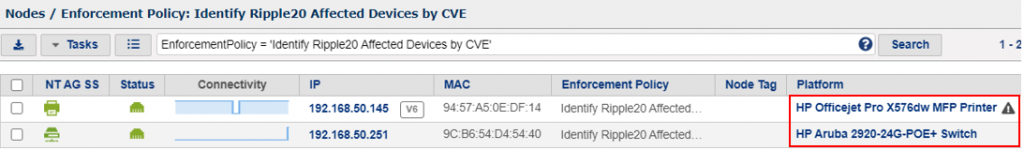
To identify these devices, we will create a Node Group and Enforcement Policy in the Genian NAC UI. The Node Group will list the 19 Ripple20 CVEs and the Enforcement Policy will allow for options later on for isolating or restricting the devices. In this example, as in the previous blog post, we will not restrict permissions since we are just auditing to locate vulnerable devices.
Ripple20 CVE Node Group
Ripple20 CVE Enforcement Policy
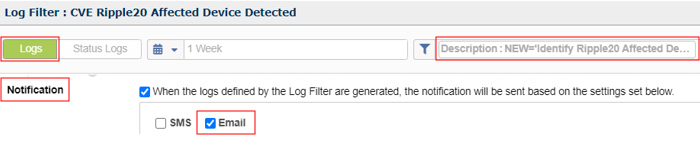
Step 2: Configure Notifications & Node Tagging
Notification
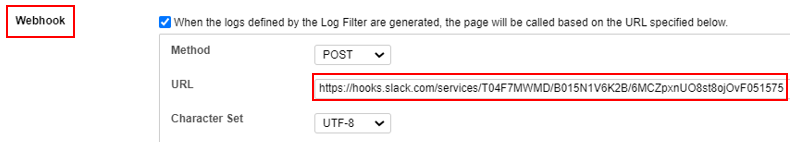
Webhook
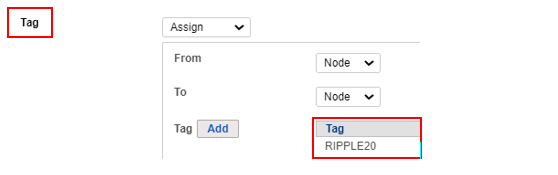
Tag
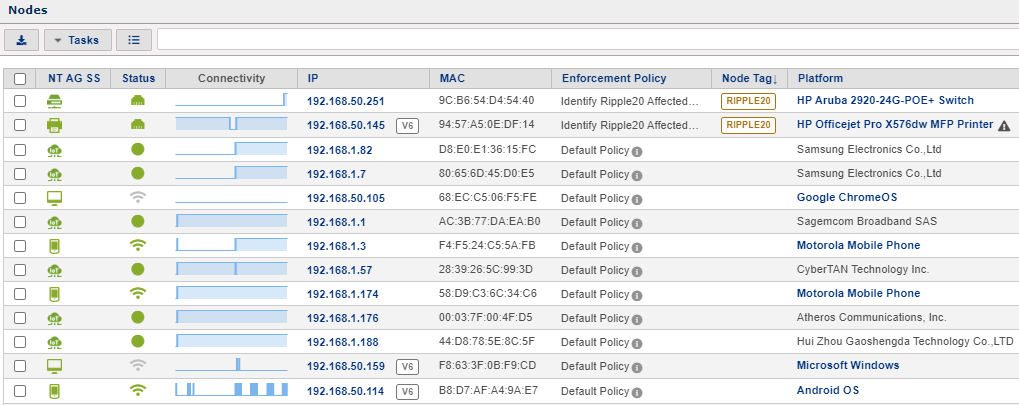
Step 3: Validate Node Tagging
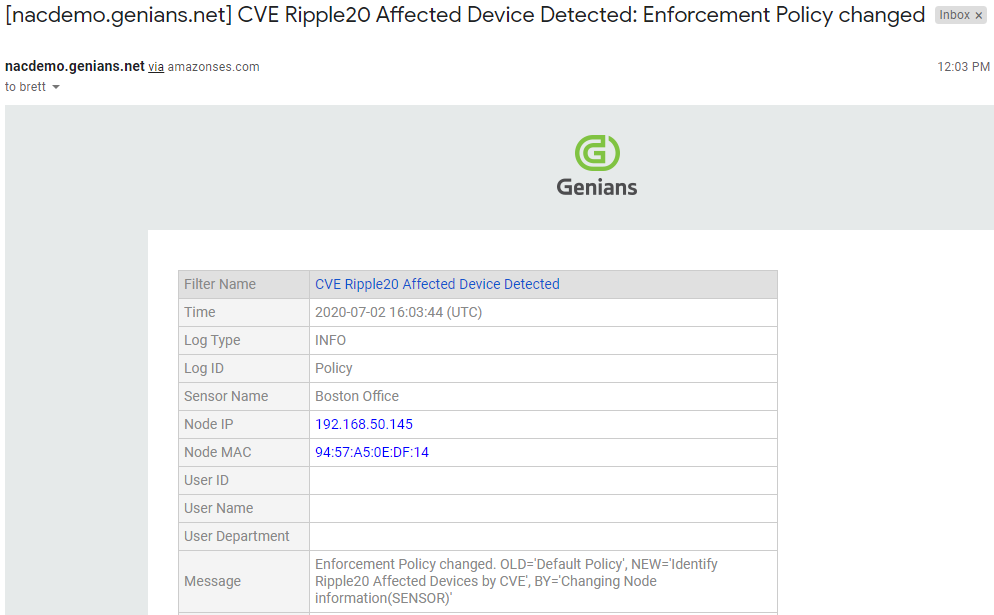
Step 4: Validate Notifications
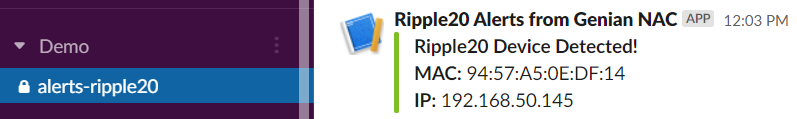
Utilizing the Genian NAC Webhook Integration for Slack, when we check the integrated Slack channel, we see that notifications are being received in Slack as well any time this event occurs.
Whether you opt to use the Device Platform as a way to check for Ripple20 devices or the CVE list as demonstrated above, the ability to rapidly deploy a Genian NAC physical or virtual Sensor, group and tag affected nodes on the network and fully automate notifications via any number of collaborative tools is a huge time saver.