Today, the Internet is a vast network of connections: people to people, people to Things, and Things to Things. This is a complex melting pot of security and network management challenges because of the convergence of technologies. How successful are you in managing your network security with this Internet of Things (IoT)? If you are struggling to keep up with the technology changes of today, how prepared will you be for the changes of tomorrow? Gartner says the IoT-installed base will grow to 26 billion units by 2020. For many organizations, that is a technological tsunami.
Today, the Internet is a vast network of connections: people to people, people to Things, and Things to Things. This is a complex melting pot of security and network management challenges because of the convergence of technologies. How successful are you in managing your network security with this Internet of Things (IoT)? If you are struggling to keep up with the technology changes of today, how prepared will you be for the changes of tomorrow? Gartner says the IoT-installed base will grow to 26 billion units by 2020. For many organizations, that is a technological tsunami.
Risks Of The Unknown, Rogue, And Legacy Devices
IT/Network administrators often are not even aware of what those ”Things” are, what they are doing, who is using them, and how they are being used on the network. It is also difficult to share contextual data between other security assets on your network, as well as refine the data to be more meaningful to your business stakeholders. Much of this ambiguity can be traced to legacy devices that make up the backbone of your IT infrastructure. These legacy devices may introduce new problems because they are older devices being integrated into more modern network environments
 Consider that even the US government is acknowledging the risks that legacy devices bring to networks of every size. In the 2016 Information Technology report put together by the United States Government Accountability Office and presented to the House Committee on Oversight and Government Reform, it is stated that the government must do more to modernize its equipment. “Federal legacy IT investments are becoming increasingly obsolete: many use outdated software languages and hardware parts that are unsupported. Agencies reported using several systems that have components that are, in some case, at least 50 years old.” The report stated even floppy disks are still in use!
Consider that even the US government is acknowledging the risks that legacy devices bring to networks of every size. In the 2016 Information Technology report put together by the United States Government Accountability Office and presented to the House Committee on Oversight and Government Reform, it is stated that the government must do more to modernize its equipment. “Federal legacy IT investments are becoming increasingly obsolete: many use outdated software languages and hardware parts that are unsupported. Agencies reported using several systems that have components that are, in some case, at least 50 years old.” The report stated even floppy disks are still in use!
These unknown and legacy devices that are still hanging around can be easily exploitable access points for those with malicious intent. While this is clearly a major issue for governments, your small business is in the same position. Not only can legacy systems open you up to security risks, but they could also be holding back your business. If you are limited by your hardware from competing with newer firms, your business can suffer. Unlike start ups with their brand new systems and investment money, existing small businesses can’t just tear up their entire IT infrastructure and start again. They need solutions that work with existing systems but also help bring everything up to modern standards to face the complex challenges businesses face.
Even in the retail industry, firms that rely on Point of Sale (POS) systems to power their business face their own issues when dealing with legacy devices. Consider the story of POS system supplier Nextep being compromised due to issues stemming from unsecured legacy devices. Having your customers’ credit card information leak due to a security breach may be an event that your business cannot survive. While businesses like Target may be able to weather the storm, small businesses often don’t fare quite as well due to the disparity in financial situations.
So, what can an IT manager do to protect one’s business and customers? The answer is a next-generation NAC solution.
The Next Generation Of NAC For Your Business
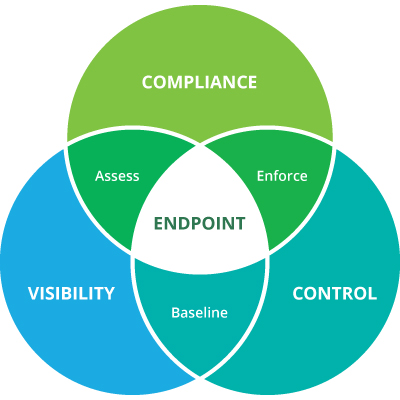
Today, an effective and dynamic Network Access Control (NAC) solution is essential for detecting and controlling these Things as they attempt to connect to your network. A next-generation of NAC solution is like having a strong front line of defense. Any system activity gets picked up and the appropriate action is taken to protect your IT network. Genian NAC is a robust solution that takes a multifaceted approach to offering full visibility and management of your IT infrastructure.
Gaining visibility into your network in real-time is extremely critical. That’s why Genian NAC was developed with smart visibility in mind to make managing your IT network painless.
Identify all devices no matter what
Genian NAC can illuminate everything on your network in real-time using smart, non-disruptive sensing technology. For smart visibility, Genian NAC uses contextual-factor identification methods utilizing the following elements:
- User: Name, Role, Credential (Email). Standards-based authentication, such as Active Directory, RADIUS, 802.1X and integration with external user databases (Oracle, MySQL, MSSQL, CSV)
- Things (Endpoints): Device Name, Type, Platform (OS), Apps, Services, MAC
- Connectivity: IP, VLAN, SSID, Switch Port, bandwidth, Access logs
Classify all detected devices whichever you want
Genian NAC organizes identified users and devices into logical groups based on your business requirements:
- 140 different classification criteria to set up logical groups dynamically.
- All classified data is conveyed into the Genian NAC policy server runs an extensive database that maintains a wide range of network-enabled device types (over 20,000) including mobile device manufacturers such as Apple, Blackberry, Huawei, LG, Microsoft, Samsung, Sony, Xiaomi, and more. This also extends to POS systems and other specialized hardware that requires network access to function.
With the smart visibility provided by Genian NAC you are now ready to manage your network more efficiently. Want to learn even more? Stay tuned to this space. Our next post will explain even more.