If you’re a network administrator, you’re probably already aware of the recent publication of remote code execution and denial-of-service vulnerabilities impacting Windows Platforms:
From Microsoft Security Response Center:
- CVE-2021-24074 (IPV4 RCE)
- CVE-2021-24094 (IPV6 RCE)
- CVE-2021-24086 (DOS)
While as of Feb 12 2021 the specific details of these vulnerabilities remain reserved by MITRE, Microsoft had already released fixes for these issues on February 9th. This raises the simple question: “Are my Windows machines up to date?” Depending on how your organization manages patches, possibly. Perhaps a more meaningful question is: “Is my network team aware of what Windows Machines are still vulnerable?”
In the case of vulnerabilities that may be easier for threat actors to exploit, having awareness throughout your technical teams, and the ability to respond on multiple levels is key. Genian NAC and Genians Endpoint Agent can be part of your strategy.
Setting Your Windows Patch Requirements
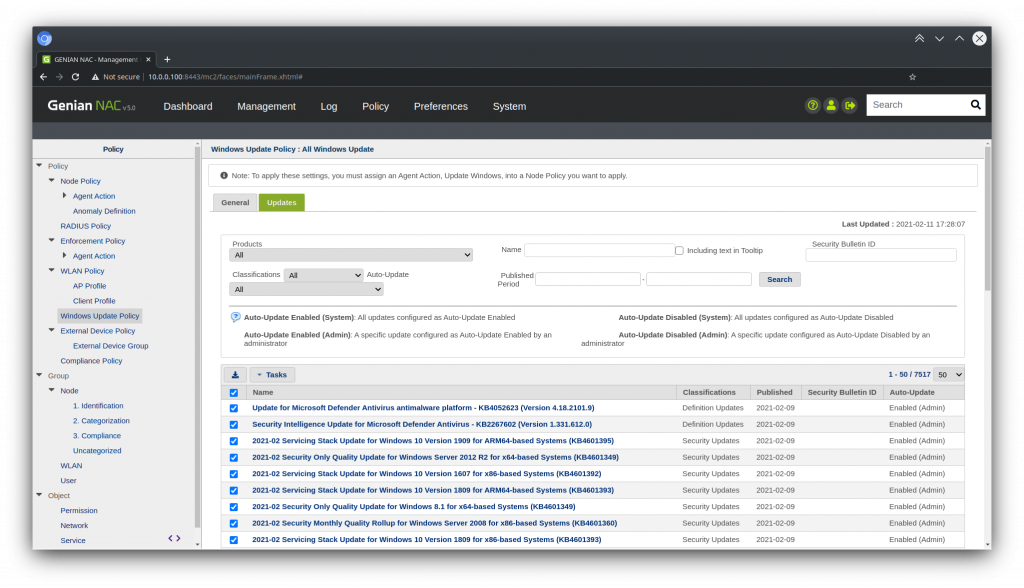
Navigate to the Policy tab in the Genian NAC web console and select Windows Update Policy. Use the Task button to create a new policy. Configure which product families, and which update classifications you wish to mandate, as well as an optional Update Delay. This delay will give you time to manually confirm which updates will be considered as required, or automatically installed by the Genians Agent.
After Creating the policy, select it from the list, and navigate to the Updates sub-tab. Use the search features to filter individual patches. Use the checkboxes and the Tasks menu to pre- authorize(Enabled) or exempt(Disabled) patches from the Auto-Update Queue.
- Updates that have a published date within the Update Delay period are temporarily set to disabled. They are reassigned according to the General Preferences after the Update Delay has passed, or if they are reassigned by an administrator.
- Any patch set to Auto-Update will be checked for, but only installed if the Genians Agent is configured to install the updates.
Scoping your Patch Requirements
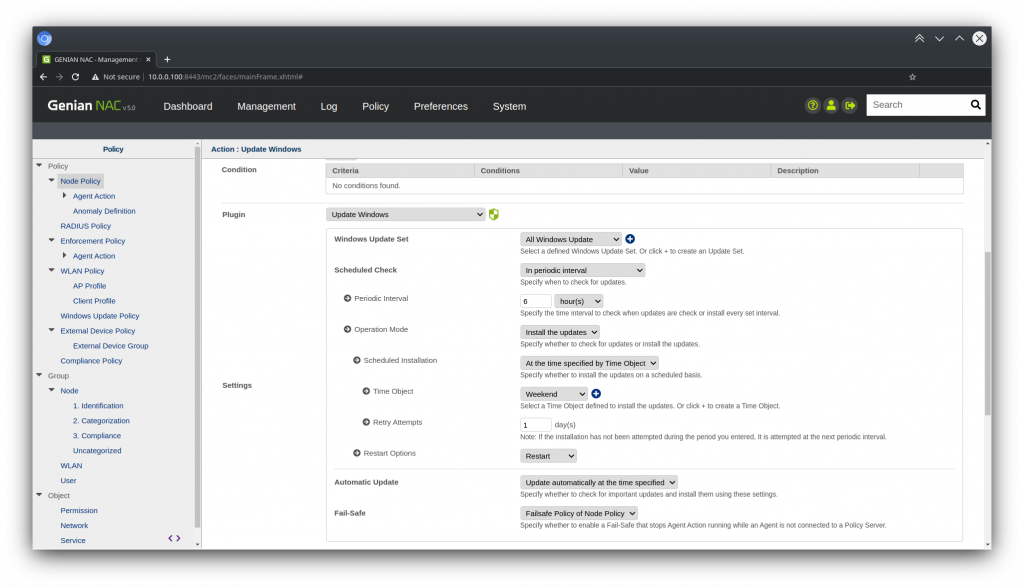
Navigate to the Policy tab in the Genian NAC web console and select Node Policy. Select a Node Policy that is linked to the Node Group(s) you want to manage, and add the Update Windows Agent Action. Continue on below:
Configuring Monitoring and Updates
Click the Update Windows Agent Action, and select which Windows Update Policy to use, as well as if you want to check the endpoints update status, or to to check and install the updates required by your policy. You can also configure additional options such as timing, and system restart.
Click Update, then click Apply.
Checking Patch Statuses
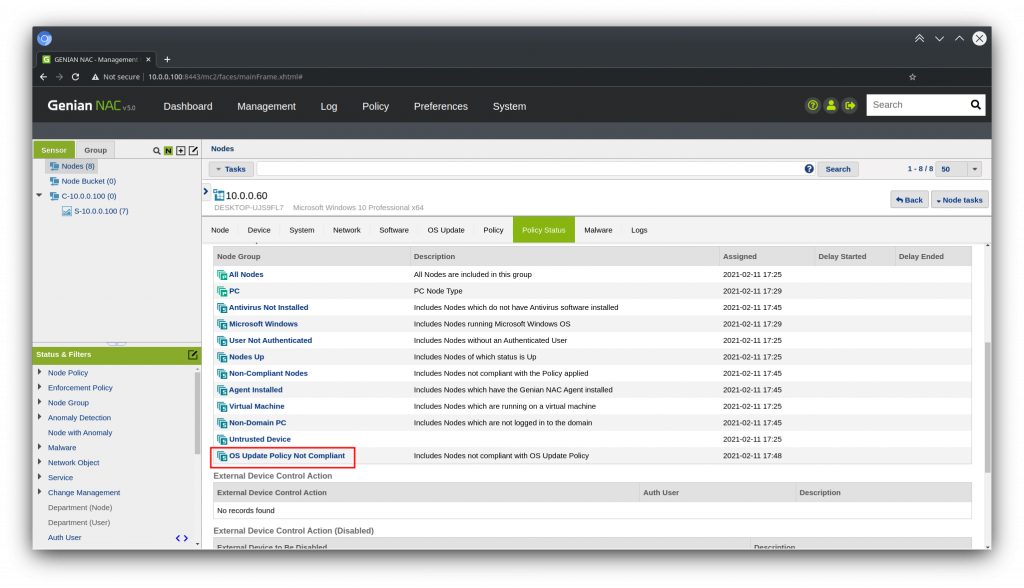
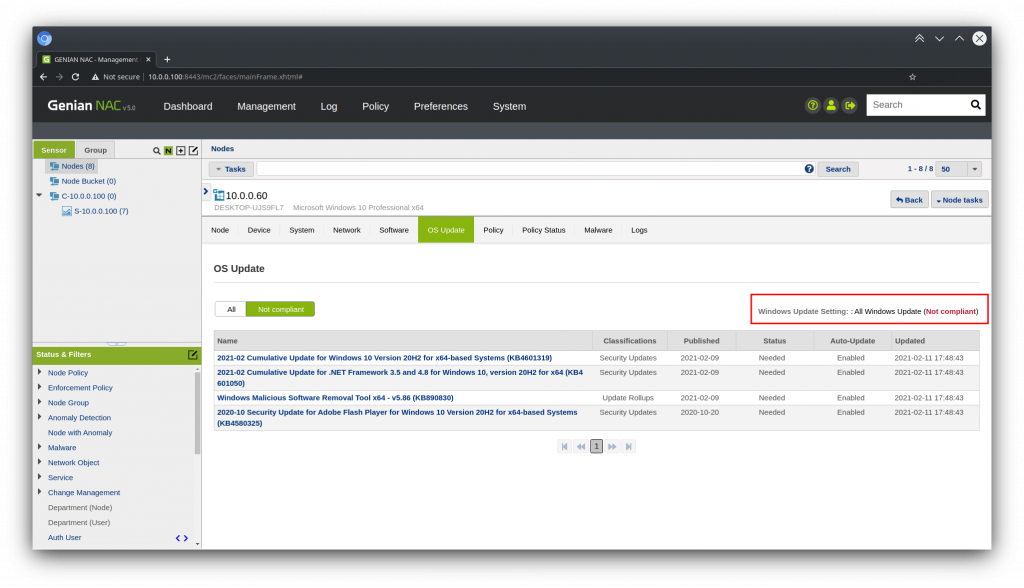
Checking under a Specific node
Go to Management > Node, and Select a node.
Use the OS Update and Policy Status tabs to check what recent updates are missing, and if the node is placed into the default OS Update Policy Not Compliant group. This group can also be used as the basis for taking automated enforcement(or notification) actions in your environment.
Dashboard
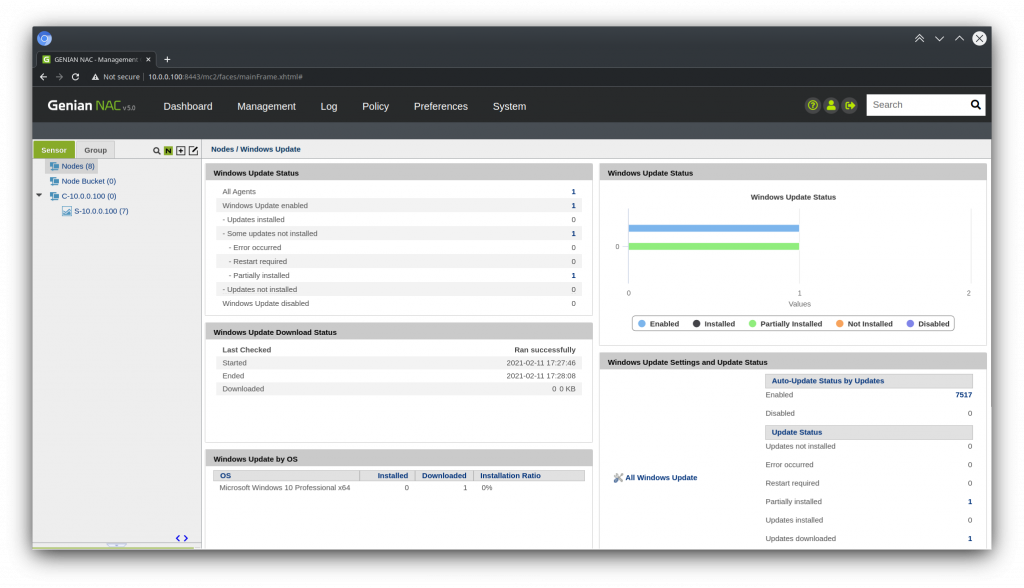
Go to Management > Node, and Select Agent > Windows Update from the Status and Filters section.
Reacting to Un-patched Nodes
Restricting Network Access
By default, Genian NAC includes an Enforcement Policy that is linked with the OS Update Policy Not Compliant group. Simply Navigate to Policy > Enforcement Policy, and select OS Update Not Compliant. Change the Status to Enabled. Configure any preferences for features like Permissions (ARP Enforcement), Captive Web Portal, SNMP switchport control, Radius CoA, or Agent based control and click Update.
Notifications and Integrating External systems
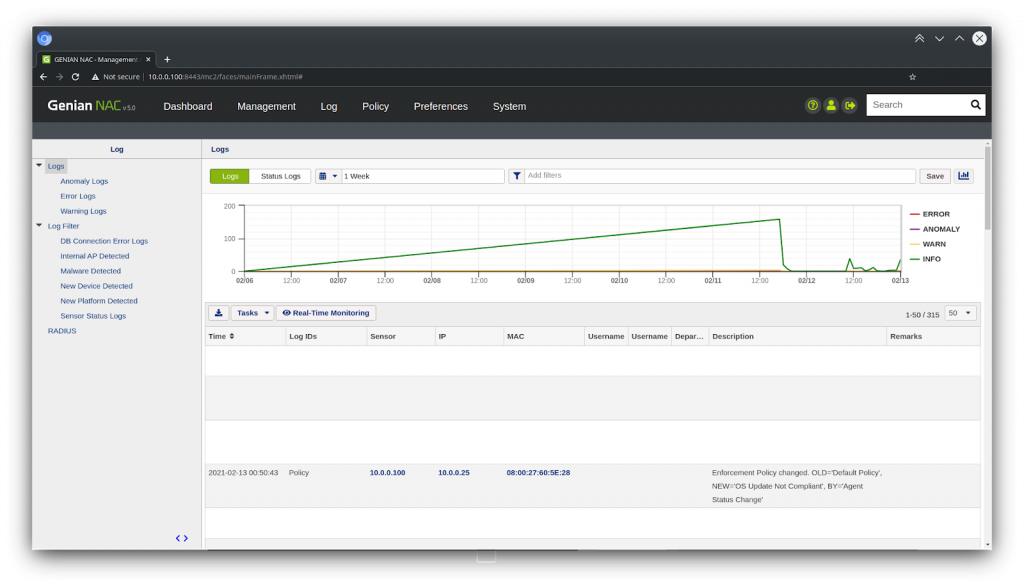
Any event that generates a log, such as the triggering of an Enforcement Policy, can be used to send outbound notifications through a variety of mechanisms, such as Email, SMS, or Webhook, making for an ideal integration with your internal communication or security systems.