The Problem – No easy way to identify affected systems
Even if you have a system in place that ensures Antivirus programs are installed, running and up to date, this scenario may leave users unprotected with no easy way to mitigate. As noted in this Bleeping Computer Article, often program updates intended to resolve one issue introduce a new issue.
“Microsoft has released a new update for Windows Defender that has broken both the Quick and Full antivirus scans. When users use these scan options, Windows Defender will only scan approximately 40 files.”
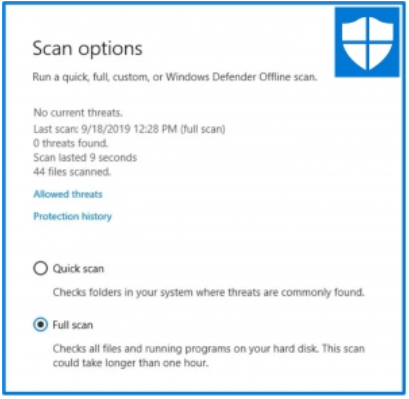
“BleepingComputer has been able to independently confirm that this is happening on our own computers that have version 4.18.1908.7 (KB4052623) installed. As you can see below, when we performed a Full scan, it only scanned 44 files and lasted 9 seconds.”
Issues like the one noted above give users a false sense of security that when they scan their system and no issues are found that their system is safe. Having unsafe systems on the network puts the entire network at risk. How can administrators quickly and easily find systems impacted by bugs such as these? Additionally, how can they easily notify end users and mitigate risk?
The Solution – Genian NAC Node Grouping and Agent Actions
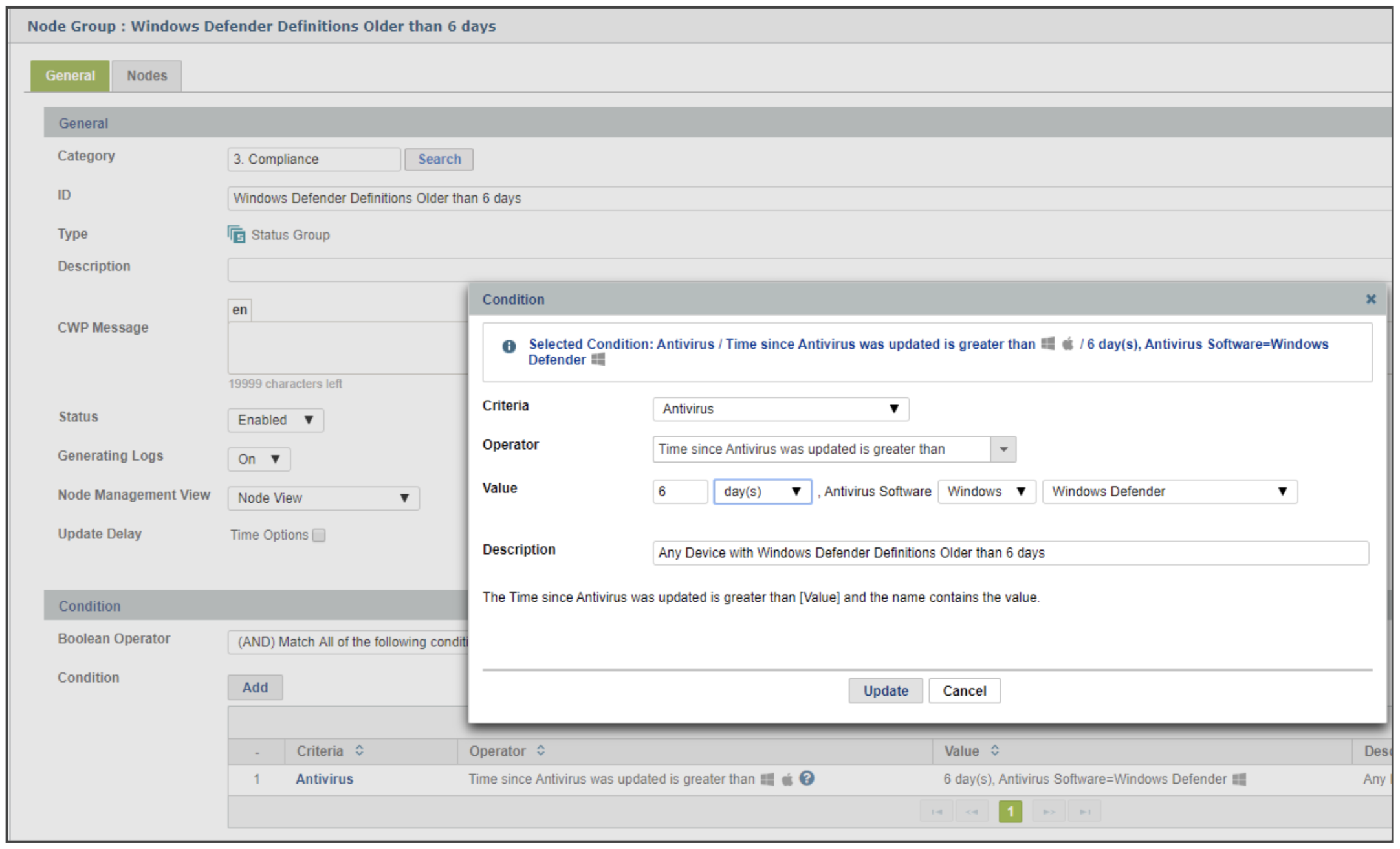
When instances like this occur, having a method to quickly identify devices that are on the broken version is crucial. The Genian NAC Agent has over 50 plugins ranging from OS, hardware and software to user accounts, screen lock, power options and everything in between. Genian NAC can also group devices together with over 500 possible conditions available to categorize devices and enforce policy.
With the Node Group feature, along with information collected by the Agent, Administrators are able to quickly create a group to identify these devices by entering the appropriate criteria as seen in the image below:
“Update 9/18/19 7:28 PM: Microsoft has told BleepingComputer that the issue has now been resolved. It turns out it was an issue in the definitions and has been resolved in “Security Intelligence Update for Windows Defender Antivirus – KB2267602 (Version 1.301.1684.0)”.
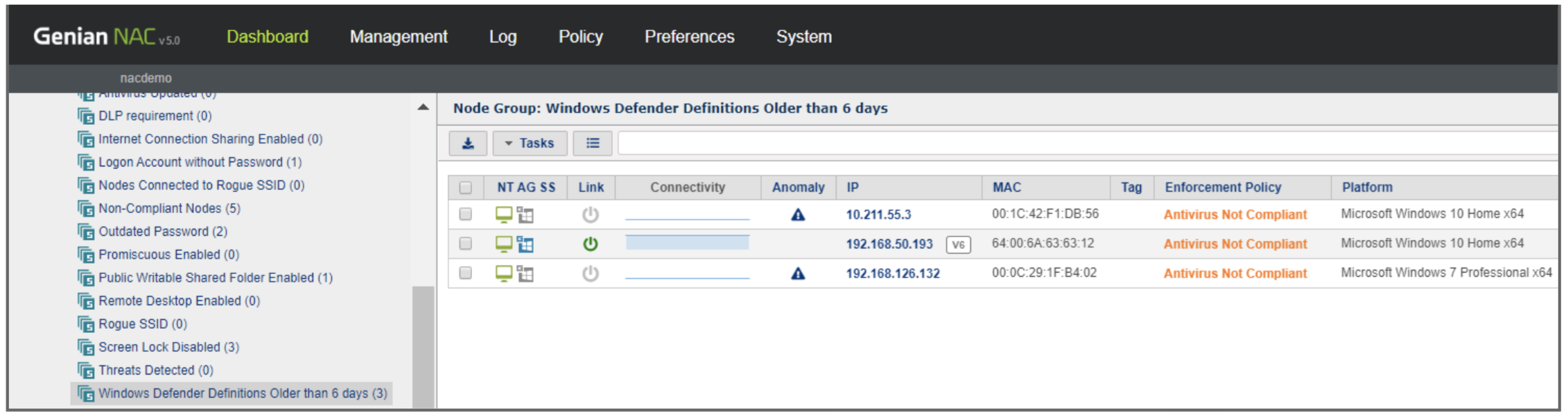
Since the article mentions a fix was issued on 9/18, the Node Group configured above will display any devices which have not had definitions updated in the last 6 days. A quick view of the new Node Group in the Dashboard shows 3 devices which fall under this category:
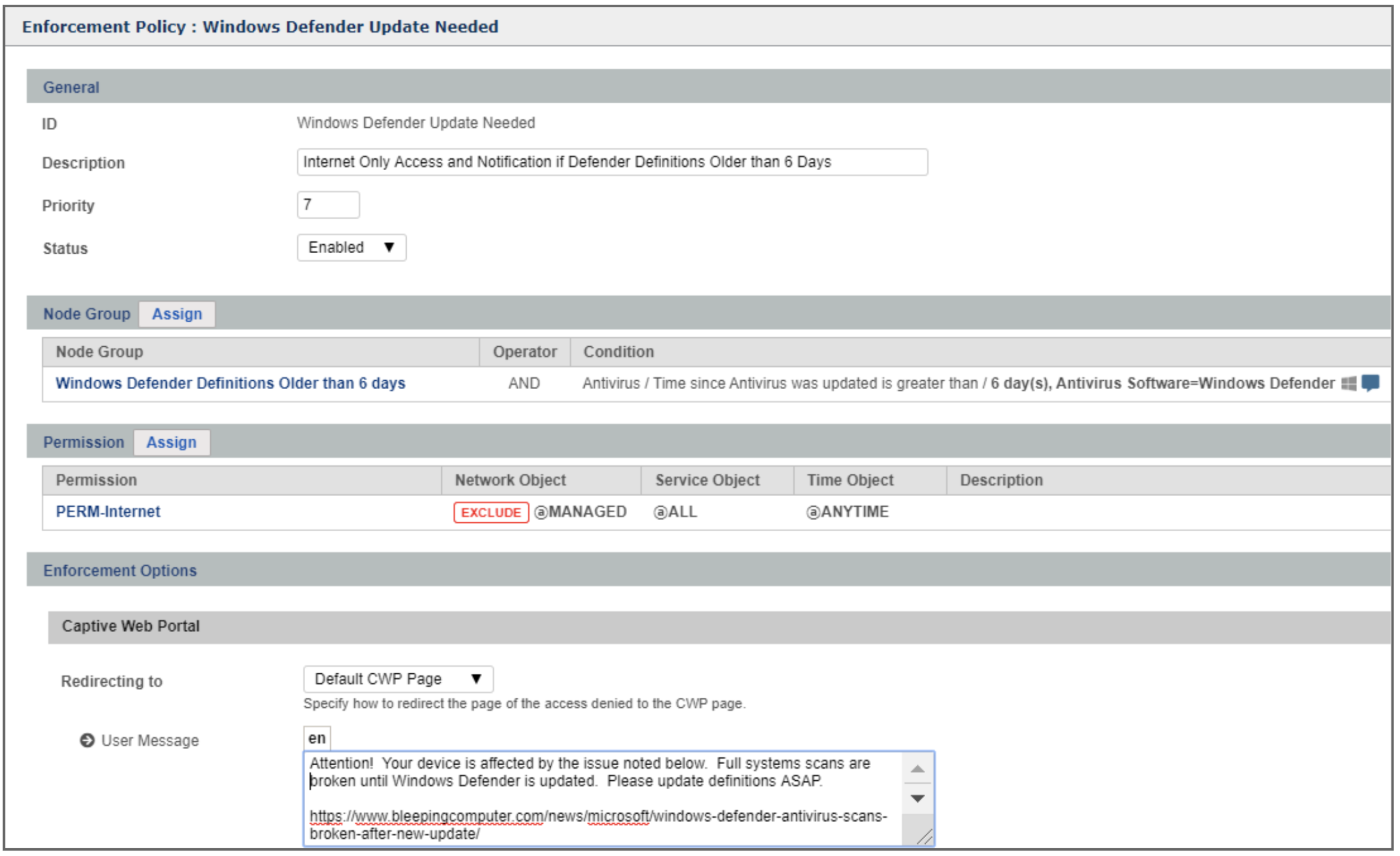
Having now identified the systems affected by this issue, Administrators can optionally take additional actions via Enforcement Policy. Notifying end users or even restricting access to Internet only until the definitions have been updated are two possible options as shown in the example below:
The example in this article is one of many which illustrates how, in addition to providing essential Network Access Control functions including visibility via Device Platform Intelligence (DPI), ensuring all devices are properly authenticated before accessing the network and assigning granular permissions through micro-segmentation, Genian NAC adds additional value. It is also an essential security tool which can help identify at-risk devices as new issues are reported in the Cybersecurity community and provide the means to quickly notify users and mitigate risk.