In today’s dynamic work landscape, the concept of the traditional office has undergone a profound transformation. The rise of remote work arrangements, including Work From Home (WFH), and the emergence of hybrid work models, have reshaped how employees access company resources.
A notable facet of this transformation is the prevalence of employees supplying their own devices (BYOD) to access campus networks, whether they’re at home, in the office, or on the go.
As organizations adapt to this new hybrid work paradigm, enterprise cybersecurity faces a host of unique challenges. This article delves into the critical cybersecurity issues surrounding remote access, with a particular focus on the experiences of hybrid workers. We explore the vulnerabilities of remote endpoints, the imperative for stringent access controls, and the evolving cybersecurity strategies essential for safeguarding sensitive data and network resources in a world where employees often transition between personal and corporate devices.
BYOD, BYOC, BYOE, CYOD born in chaotic cybersecurity climates
Back in the early 2010s, the concept of BYOD began to gain popularity as personal devices such as laptops, mobile phones, and tablets were being used increasingly for work purposes. Even though BYOD offered employees greater flexibility to access company networks, one of the main issues that arose was the potential for increased security risk. Indeed, allowing employees to use their personal devices for work-related tasks presented several security challenges, including:
- Remote Access: When employees access company resources remotely from their personal devices via VPN, they are implicitly trusted with broad access to company resources, which increases the attack surface and creates serious security risks.
- Device Diversity: Employees may use a wide range of devices with different operating systems, security configurations, and patch levels. Managing and securing this diverse device landscape can be complex.
- Unauthorized Access: Employees might not secure their personal devices with strong passwords or they may use inadequate security measures, making it easier for unauthorized individuals to access company resources.
- Data Loss: Personal devices can be lost or stolen, potentially leading to the loss of sensitive company data if not adequately protected.
- Malware and Phishing: Personal devices may not have the same level of security software or corporate email filtering as company-issued devices, making them more susceptible to malware and phishing attacks.
- Compliance Concerns: Companies in regulated industries must ensure that data on personal devices complies with industry-specific regulations, which can be challenging to monitor and enforce.
As NIST (the National Institute of Standards and Technology) Special Publication 800-207 points out: “Zero trust is a response to enterprise network trends that include remote users, bring your own device (BYOD), and cloud-based assets that are not located within an enterprise-owned network boundary. Zero trust focuses on protecting resources (assets, services, workflows, network accounts, etc.), not network segments, as the network location is no longer seen as the prime component to the security posture of the resource.”
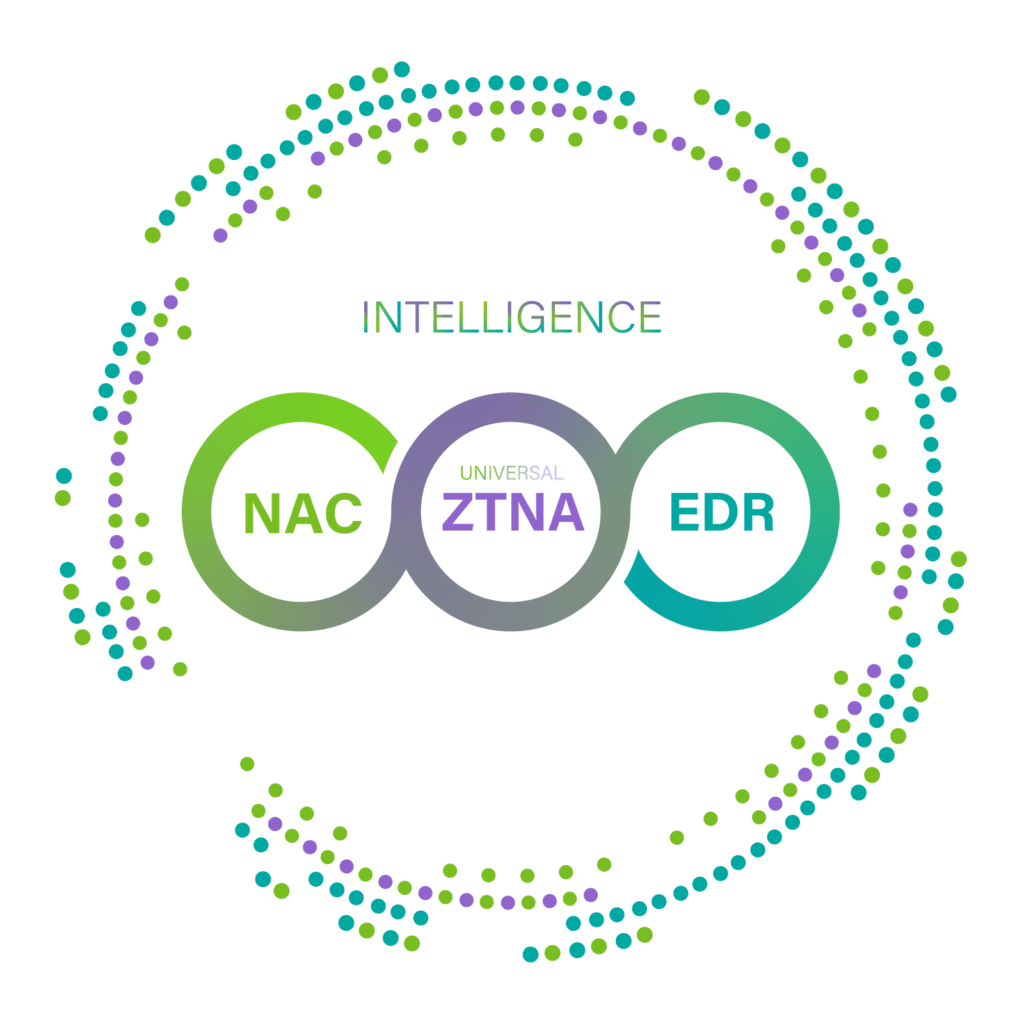
NAC-driven ZTNA born to address these challenges
To address these issues, Genians strongly advises leveraging Zero Trust Network Access (ZTNA) empowered by Network Access Control (NAC), which significantly enhances BYOD cybersecurity by providing a robust framework for securing network access seamlessly from campus, remote, cloud, and hybrid environments. Here’s how you can use ZTNA to address BYOD cybersecurity challenges:
- Deploy Identity and Resource based Microsegmentation: To achieve a more granular degree of visibility and access control for BYOD devices, network managers need to develop logical groups based on identity and resource type (assets, applications, services, workflows, network accounts); this will also result in the securing of targeted devices and mitigate the potential impact of security breaches on sensitive systems. By enforcing device isolation, ZTNA ensures that BYOD devices can access only specific segments of the network, limiting their exposure to sensitive areas accordingly.
- Implement Explicit Access Controls: ZTNA enforces strict access controls based on user identity, device trustworthiness, and other contextual factors. Integrate ZTNA solutions to ensure that only authorized users and devices can access your network and resources. ZTNA will mitigate the risk of lateral movement by implementing layer 2-based access control.
- Verify Device Trustworthiness: ZTNA evaluates the security posture of devices attempting to access network resources. This includes checking for up-to-date operating systems, security patches, antivirus software, and compliance with security policies. BYOD devices must meet these criteria to gain access.
- Employ Granular Access Policies: Define granular access policies within your ZTNA solution. This allows you to restrict access to specific applications or data based on user roles and responsibilities. For BYOD users, this means they are only able to access exactly what’s necessary for them to do their job.
- User Authentication: Implement strong authentication methods, such as multi-factor authentication (MFA), including biometric authentication and smart card options to ensure that users are who they claim to be before granting access to corporate resources.
- Continuous Verification: Continuously monitor user and device behavior and security compliance status across all active sessions. If any anomalies or suspicious activities are detected, access can be revoked in real-time to prevent security breaches.
- Data Encryption: Require that all data transmitted between BYOD devices and corporate resources be encrypted. This means protecting data in transit as well as at rest and is critical to ensuring data confidentiality.
- Remote Wipe and Lock: Integrate remote wipe and lock capabilities with Mobile Device Management (MDM) solutions in your ZTNA solution. This allows you to remotely erase sensitive data from BYOD devices in case of loss, theft, or when an employee leaves the organization.
- Compliance Alignment: Use ZTNA to enforce access controls and security policies that align with industry-specific regulations and compliance requirements. ZTNA helps organizations demonstrate compliance with data protection standards.
- Regular Auditing and Reporting: Conduct regular audits and generate reports on BYOD device access and security compliance to ensure that policies are being enforced effectively.
- Privacy Considerations: Ensure that your ZTNA implementation respects employee privacy by limiting access to personal data on BYOD devices to what is necessary for work-related tasks.
- Flexible and Secure Onboarding Process: NAC-driven ZTNA can orchestrate above to strike a balance between empowering employees to use their preferred devices for work and ensuring the organization’s security, compliance, and data protection requirements are met.
By integrating NAC-driven ZTNA with your BYOD cybersecurity strategy, you can create a secure and flexible environment that allows employees to use their personal or company-owned devices for work without compromising security. This approach ensures that access to corporate resources is based on trust, continuous monitoring, and strict security policies, reducing the risk of data breaches and other security incidents.
That said, integrating ZTNA with BYOD can still involve facing an array of challenges,such as deployment complexity, device compatibility, the high cost of maintenance, and privacy and user experience concerns. Genians NAC-driven ZTNA can address these challenges without disturbing IT security operations and without breaking your budget. Sign up now for a 30 day free trial or conf call to discuss further.