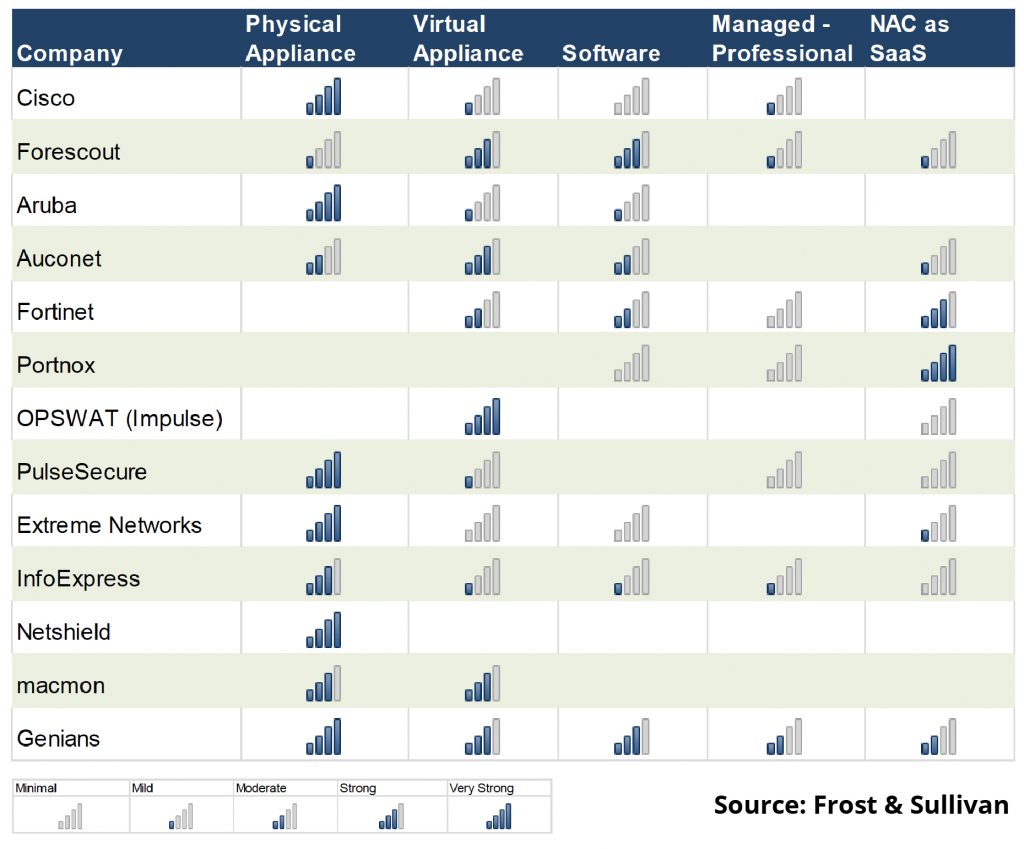
Frost & Sullivan’s “Global Network Access Control Market, Forecast to 2024” indicates that NAC has become an important element in the development of Zero Trust Networks (ZTN) as it provides visibility, monitoring, and control at the network access layer.
Gartner’s May 2020 Market Guide for Network Access Control also points out, “Most organizations interested in NAC are looking to establish the security of devices and users accessing the network, driven primarily by audit findings and to some degree a zero-trust network security strategy.” So NAC works as a foundation for cybersecurity at the access layer. It also provides a segue for zero-trust security.
Indeed, NAC is the critical technology that orchestrates other core technologies to maximize cybersecurity effectiveness while achieving ZTN. To support this outcome, NAC vendors need to provide flexible deployment options based upon strong software capabilities. Even though network infrastructure is evolving quickly, many organizations still maintain legacy or hybrid environments. NAC can be delivered via a physical or virtual appliance or even in a service format.
Which deployment options are available?
The chart by Frost & Sullivan summarizes how each NAC vendor is pursuing the market with different solutions.
Genians can Deliver
Genians has delivered enterprise-grade NAC solutions in various formats to 1,600 customers around the world since 2005.
- Software: Genians’ NAC software comes in an all-in-one format, providing both a Policy Server and a Network Sensor. Network sensor software may be installed individually. It can be installed in any Intel-based virtual or physical machine. The Policy Server distributes established policies to Network Sensors and orchestrates seamlessly with third-party security solutions. The Network Sensor monitors wired, wireless, and virtual networks and provides complete control over endpoint device traffic via ARP, TCP, UDP, SSID etc. by eliminating the need for complex configurations and network changes. The software can be freely downloaded from Genians’ website. Up to 300 devices can be monitored without a license or trial period.
- Physical appliance: Genians provides an out of band NAC solution powered by its Network Sensor. Should a higher level of security be required by keeping all NAC components within the network, this option should be considered. Indeed, Genians’ customers in government, military, and financial institutions primarily use this option. Genians’ NAC policy server comes with 3 major built-in services (DHCP, RADIUS, Syslog), allowing it to cover 802.1x networks effectively.
- Virtual appliance: Genians NAC can be also installed on a virtual machine. Support is provided for various hypervisors, such as VMWare, VirtualBox, and XenServer.
Managed NAC: Genians’ Policy Server can be operated in the Genians Cloud on AWS, or on other public cloud services such as Azure or GCP. MSSP and professional service providers can easily manage their customers’ policy services in a central location by plugging Genians NAC into their respective cybersecurity stacks. They also have the option of using their own equipment as Network Sensors. - NAC as a Service: Genians’ Policy Server supports multi-tenancy environments (e.g. Docker containers) while the Network Sensor can support universal customer premises equipment (uCPE). Genians’ comprehensive management service encompasses:
- Management one-stop service (sites, users, licenses, subscriptions, billing)
- Virtual domain support
- Centralized dashboard and reporting
- Zero config provisioning
- White label service
Multiple deployment scenarios can therefore be supported by Genians’ Next-Gen NAC.
What are the essential features required?
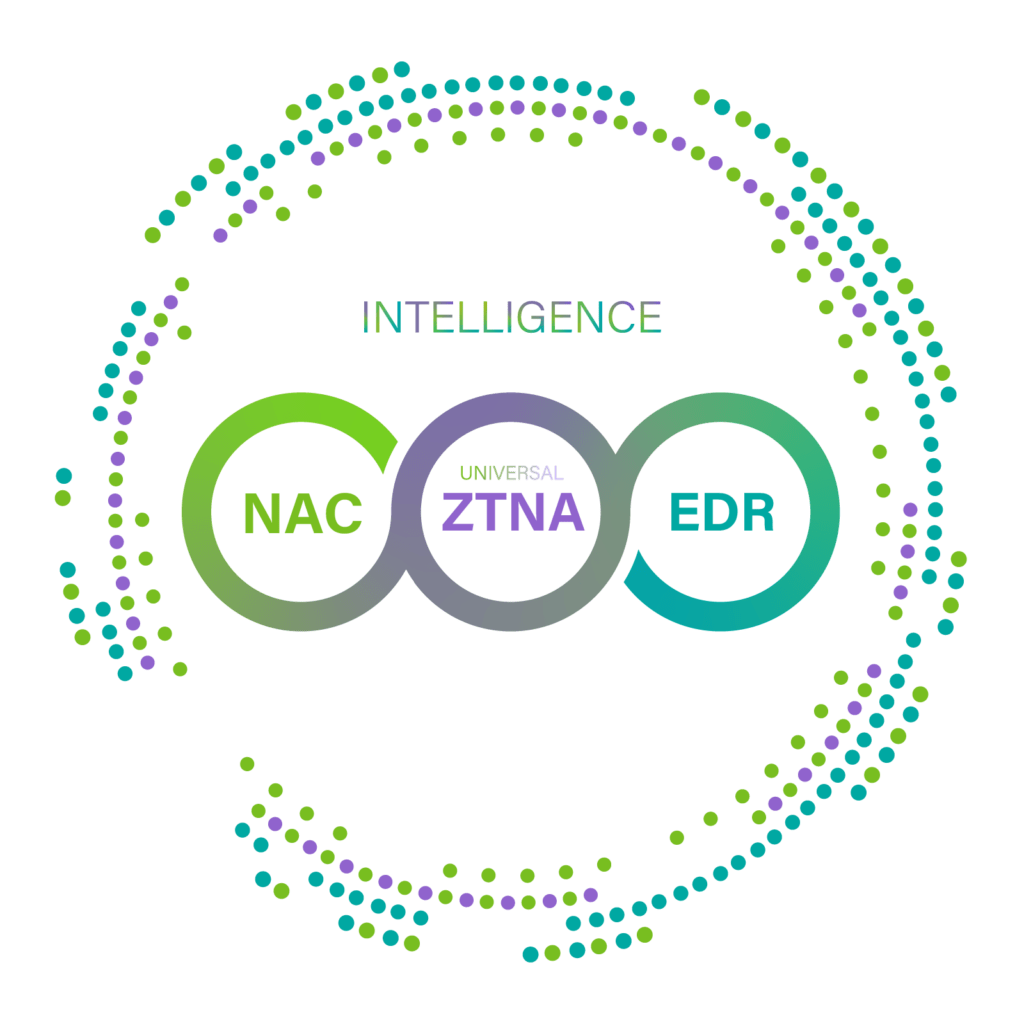
As can be seen above, Genians does not rely on a single visibility or control method; rather, it provides multi-layered Access Control by utilizing the benefits provided by each of the following:
- Layer 2: ARP Enforcement (using Network Sensor)
- Layer 3: TCP reset (using Mirror/SPAN Sensor)
- Layer 3: Inline Enforcement (Dual-homed Gateway)
- Agent: NIC/Power Control, Alert Popup
- Integration: Firewall, Switch port shutdown (SNMP, Webhook)
- Built-in Services: DHCP, RADIUS, Syslog
In short, you can choose one or more of the above options to fortify your network cyber-defense environment based on your requirements and deploy NAC programmatically from visibility, to access control, to automation. Further, Genians DPI and multi-layered access control provides enhanced visibility for IoT/industrial IoT (IIoT) environments by providing for integration with software-defined perimeter (SDP) and other security technologies.