Kyeyeon Kim
Kyeyeon Kim is the Co-founder and CTO of Genians, bringing over two decades of expertise in network security and open-source technologies. As a pioneer in South Korea’s IT industry, he has led the development of Genians’ Network Access Control (NAC) solutions. Prior to founding Genians, Kyeyeon played a pivotal role in launching Yahoo’s services in South Korea as Chief Engineer. He also served as Director of Development at Oullim Information Technology, where he was instrumental in developing successful firewall and VPN products. Kyeyeon’s extensive experience encompasses software development and IT solutions, reflecting his commitment to advancing cybersecurity technologies.
Korea is moving beyond compliance. In response to nationwide cyber incidents, the government has transformed…
At RSAC 2025, AI and trust stood out as key themes in securing both systems…
Discover the best way to gain comprehensive network visibility by leveraging network observability rather than…
Genians Zero Trust NAC can guide you throughout on the best methods for reforming your…
Digital trust begins with getting digital identity attributes and the digital security onboarding process can…
Recent Gartner and Frost & Sullivan’s report indicates that NAC has become an important element…
By sharing what Genians learned during RSAC 2020. Genians can help to reshape the foundation…
We as Genians always work together with customers, partners, vendors, and communities to sustain our…
Genian NAC can easily identify how many Windows 7 exist including unknown or transient Windows…
Genians NAC supports the necessary balance between the dictates of compliance and an organization’s need…
This article continues our series on “Multi-Layered Access Control,” which seeks to explore various approaches…
Genians NAC can track and secure vulnerabilities in the Address Resolution Protocol (ARP)…
The New Complexity of the Connected World Today, the Internet is a vast network of…
Over the past few years, there has been much attention paid in the technology security…
As the challenges identified above manifest themselves increasingly, NAC platforms will need to be highly…
Network Access Control (NAC) is a key component of your cyber defense framework….
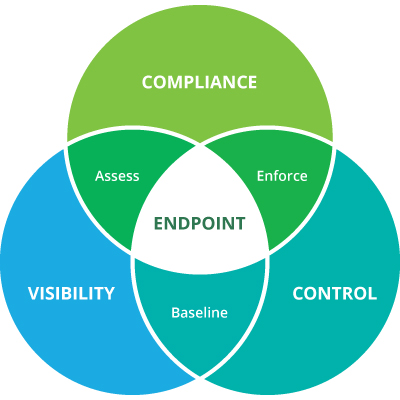
Network Access Control (NAC) ensures that all connected devices are automatically identified, classified, authorized, and…
Today, the Internet is a vast network of connections: people to people, people to devices,…
We are well into an age of decentralization. Our offices are decentralized. We work all…
Every industry experiences trends. One usually thinks of musical tastes or fashion choices, but even…
It’s rare that cybersecurity gets mainstream press, but recent events have everyone from the average…