Background: Securing the Edge of a Nationwide Network
South Korea’s largest telecommunication company, a pioneer in establishing a nationwide LTE network and a leader in developing advanced 5G and IoT services, faces the critical challenge of securing its vast and complex infrastructure. With the imperative to provide increasingly rich telecommunications capabilities in the most secure manner possible, the carrier needed to enhance visibility into its edge networks. This was crucial for ensuring the highest levels of endpoint security, network availability, and regulatory compliance.
Overcoming Security Silos and Visibility Gaps
Managing an extensive network that includes 12 IDC centers and thousands of nodes across the country, the carrier experiences a continuous stream of network access requests from employees, contractors, partners, and customers. Their existing security solutions, however, struggled to manage these requests effectively and securely. The carrier specifically sought a more comprehensive NAC solution to address:
- IT Security Silos: Fragmentation among existing cybersecurity solutions leading to inefficient management.
- Lack of Endpoint Visibility: Incomplete visibility for all IP-enabled devices (wired and wireless) across their vast network.
- Ineffective User and IP Management: Suboptimal user authentication processes and challenges with IP address management.
- Insufficient Patch & Antivirus Management: Leading to persistent endpoint security and compliance issues.
Solution: Genians’ NAC for Comprehensive Edge Control
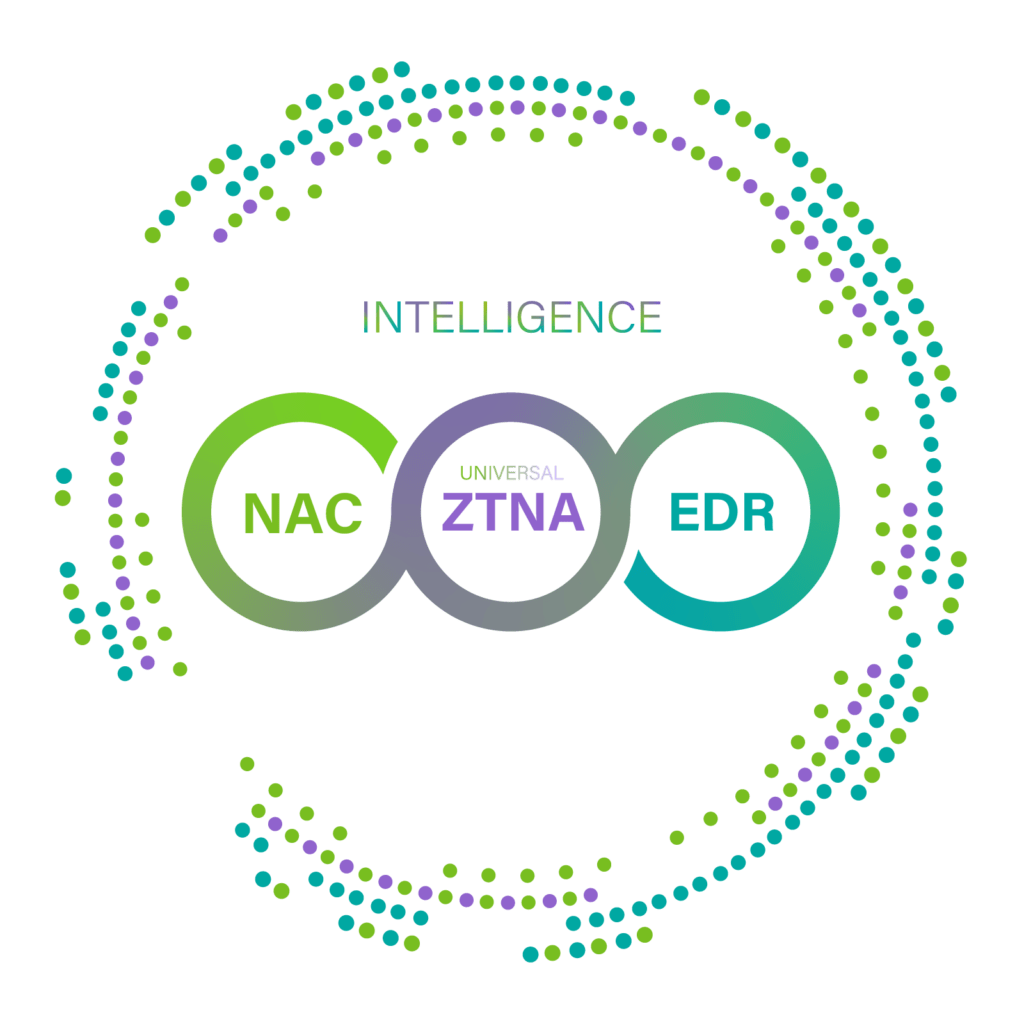
Genians provided the carrier with its most comprehensive Network Access Control (NAC) solution, delivering end-to-end visibility and secure access control. Genians’ NAC capabilities inherently offer essential IT management solutions, including IPAM, Endpoint Configuration Management, Switch Port Management, WLAN security, and BYOD support, right out of the box.
Genians enabled the carrier to:
- Consolidate Security: Eliminate security silos by replacing multiple legacy IT security solutions and seamlessly integrating with other critical systems.
- Achieve 360º Visibility: Gain a real-time “bird’s-eye view” of all IP-enabled devices using Genians’ non-disruptive sensing technology, eliminating network blind spots.
- Enhance Device Intelligence: Increase device detection accuracy via Genians’ Device Platform Intelligence (DPI) without requiring agents. This intelligence correlates contextual data to improve security policies by providing:
- Accurate device platform identity.
- Contextual access information (Who, What, Where, When, How).
- Business context related to devices (e.g., EOL, EOS, Manufacturer Info, CVEs).
- Detection of anomalies from inside the network.
- Improve IP Address Management (IPAM): Streamline managing static IP/MAC addresses, preventing IP conflicts, and provisioning IP addressing via an on-demand service.
- Consolidate User Authentication: Unify authentication processes for both wired and wireless access.
- Automate Endpoint Compliance: Ensure timely installation and maintenance of all required software and patches, control peripheral devices (like USB and Bluetooth), and enforce Windows security settings.
- Secure Onboarding & Isolation: Provide a safe and secure onboarding process for Guest and BYOD scenarios, while proactively blocking and isolating unknown, unauthorized, insecure, or rogue devices from the network.
- Ensure Audit Readiness: Provide a complete audit trail for all IP-enabled devices to demonstrate compliance and generate comprehensive audit reports.
Summary: Network Intelligence, Cost Savings, and Unrivaled Compliance
The carrier now derives enhanced intelligence from its network edges, enriching the profiling of all devices associated with users, data, applications, and services. This enables more effective granular policy management and dynamic access control.
Elevating Endpoint Compliance and Operational Efficiency
Because Genians provides essential IT management features integrated at the network edge, the carrier can significantly save costs and reduce the effort required to maintain endpoint compliance at the highest level. This comprehensive solution empowers the carrier to ensure the security, availability, and regulatory adherence of its cutting-edge telecommunications infrastructure.