Every industry experiences trends. One usually thinks of musical tastes or fashion choices, but even the world of IT security goes through phases. Let’s go back about ten years or so and remember what the IT landscape looked like at the time. Way back in 2006, we started seeing a shift that in 2016 seems almost quaint when one considers how much the workplace has evolved in that time. At that time, the new “threat” so to speak to a business’ IT network was the proliferation of laptops amongst other changes in the way we approached local area networks. If you go even further back, the typical IT set up was fairly simple in comparison to what we have now. A series of desktop computers hardwired via LAN for internet access was relatively easy to monitor and control. In 2006, we saw that change in a few ways.
Employees begin to Bring Their Own Devices (BYOD)
Desktops, while still the hardware of choice for most businesses providing their employees with a device, were beginning to lose ground a bit to laptops for the first time. Laptops sales were up and competitive with desktops. Employees could bring their laptops from home and to the office. Mobility was the new topic of conversation.
Rise of Wi-Fi
Alongside laptops came the widespread use of WLAN (wireless local access networks), specifically networking based upon 802.11 which we casually refer to as Wi-Fi now. At the time, however, Wi-Fi was moving from an emerging, bleeding-edge novelty to the preferred standard of office environments. Moving from LAN to WLAN brought new challenges to the IT security industry.
A growing interest in software-defined perimeter (SDP)
In the early 2000s, “worms” began to gain more traction and were maliciously deployed with more regularity. These bits of malware brought havoc to both individuals and businesses due to the ease of transmission. If one infected machine gained access to a business’ network, every workstation could easily be compromised.
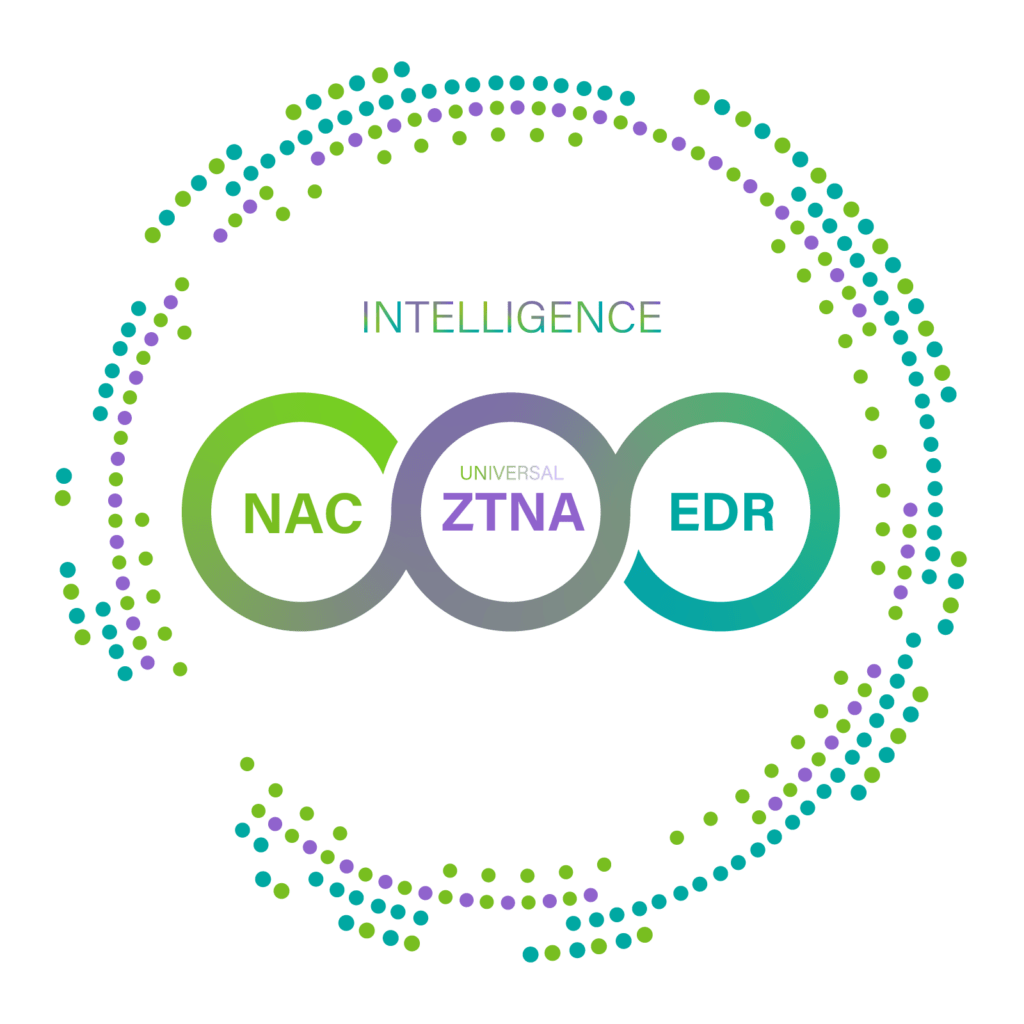
So, then the question became, “How do we defend our networks against these new threats?” The answer was Network Access Control (NAC).
Network Access Control was the solution to these increasingly complex problems. With more devices to keep track of and wireless connections being less secure, an NAC could enforce a standard that all devices needed to adhere to in order to access a network’s resources. Thanks to improved visibility, IT managers could gain greater control and mitigate the risks caused by an increasing number of variables.
In the ten years since, however, the Internet of Things (IoT) has complicated IT security even more. The changing face of network administration has caused some to call into question the efficiency of using NAC as a solution. IT professionals have been showing a growing interest in software-defined perimeter (SDP) as a solution to problems such as the need for extended visibility, context-based authentication, and granular policy enforcement. The question then becomes whether or not NAC is still the go-to solution. And if it is, can it still provide the same services while also integrating what SDP brings to the table.
As SDP gains traction, can NAC providers change with the times and integrate these desired new features into their products? Genians response is: Yes, we are ready for SDP.
Genians ready for SDP
Here is how Genians Next-Gen Network Access Control can handle today’s network security concerns:
- Broad device support: Genians runs an extensive enterprise-grade database over the cloud, which maintains a wide range of network-enabled device fingerprinting (over 20,000) including mobile device manufacturers such as Apple, Blackberry, Huawei, LG, Microsoft, Samsung, Sony, Xiaomi, and more.
- Contextual-factor identification methods utilizing the following elements:
- User: Name, Role, Credential (Email). Standards-based authentication, such as Active Directory, RADIUS, 802.1X and integration with external user databases (Oracle, MySQL, MSSQL, CSV).
- Endpoints: Device Name, Type, Platform (OS), Apps, Services, MAC, Compliance status
- Network Connectivity: IP, VLAN, SSID, Switch Port, bandwidth, access logs.
- Node Groups (like Micro segmented networks): Genians organizes identified devices/users into logical groups dynamically based on business requirements. (Genians provides over 140 different classification conditions to set up logical groups rapidly and effectively).
- Policy Group: Node-related information such as device type, address (IP/MAC), user authentication, access logs, etc.
- Status Group: Node status measured by policies and the associated conditions.
Grouping Nodes provides significant administrative benefits by organizing IT resources, simplifying compliance, and applying policies to a targeted group across the micro segmented networks. Next posting will present how exactly Genians manage and control the Node Groups (Micro segmented networks).