As noted in a recent Genians News announcement , Genians was named as a Representative Vendor in the 2020 Gartner Market Guide for Network Access Control, recognized for its Genian NAC product. The report provides NAC market definition, market description, market direction, and market analysis as well as recognizes Representative Vendors. To us, the most key take away from the report is the Market Recommendations section at the end.
The report provides market recommendations, stating “organizations should focus on total implementation cost, alignment with organization type (size and industry vertical) and integration with existing infrastructure vendors to differentiate solutions. Most organizations only need to implement a single NAC solution and therefore should seek to consolidate if multiple NAC solutions exist within their environment. Multiple NAC solutions generally occur through M&A activities or by way of complex organizations making independent buying decisions.” In this blog, we will review these recommendations and how we believe Genian NAC can help fulfill them.
Visibility Before NAC Vendor Selection
Gartner Recommendation
“Perform an initial network inventory before selecting an NAC vendor. This will influence your decision based on the capabilities of your network switches and routers, as well as help with budgeting since many NAC vendors license based on the number of IP addresses protected.”
Genians Can
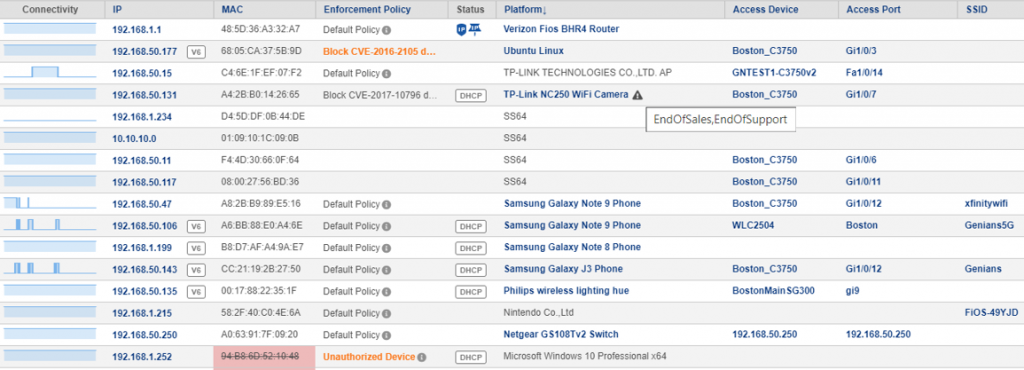
By default and without any special configuration, Genian NAC detects all IP-Enabled devices on the network non-intrusively. Network inventory/detection happens automatically once a network sensor is deployed. Because there is no dependency on complex network integrations, this allows for visibility to be obtained quickly, a key component when evaluating any solution.
Additionally, the ability to fully evaluate the Enterprise version of Genian NAC via a self-deployed free trial further facilitates the recommendation to gain visibility and evaluate a product before selecting a vendor.
Genian NAC in 10 Min (Policy Server)
Genian NAC in 10 Min (Network Sensor)
Network Access Control for Visibility, Control, and Asset Management
Gartner Recommendation
Genians Can
Providing visibility, control and automation are all core functions of Genian NAC. With Device Platform Intelligence, enhanced visibility is provided above and beyond simple device fingerprinting. With this enhanced visibility, more granular use cases can be defined allowing for more accurate control. Information such as End-of-Sale/Life, platform images and related CVEs can also then be shared with external systems via various methods such as Syslog or Webhook.
Device Platform Intelligence
DPI Demo
Security Automation for Zero-Day Threat Quarantine
Gartner Recommendation
“Use the postconnect functionality of your NAC solution. Most NAC products integrate with multiple security products. Configure NAC to automatically enforce policy when your threat detection solution (for example, network sandbox) alerts that an endpoint has been compromised. NAC can automatically remove the endpoint from the network, or it can enforce another policy that limits the endpoint’s ability to communicate externally.”
Genians Can
Security Automation is a key component of Genian NAC which allows for 3rd party integrations with IDS/SIEM/NGFW and other external systems to enhance the overall cybersecurity ecosystem. Quick and easy UI-based Syslog and API integrations extend threat intelligence to the edge enabling real-time Layer 2 quarantine of zero-day threats. Output integrations are available as well to feed information to collaboration tools and notification systems based on event logging of node activity and user authentication and access.
DNS, DHCP, and IPAM (DDI)
SIEM
Alert Notification
Network Access Control still has a critical role to play in any cybersecurity plan whether it be visibility, asset management, control/segmentation, Zero Trust or security automation. We believe that organizations should carefully consider the topics discussed in the Market Recommendations section of the Gartner Market Guide for Network Access Control when researching and choosing a solution to ensure the solution chosen is the right fight for the organization’s business, network environment, and security initiatives. These front end considerations will pay dividends on the back end.
Align NAC with ZTNA Initiatives
Gartner Recommendation
Genians Can
Genian NAC can be implemented with Zero Trust NAC policies out-of-the-box quickly and easily. With the ability to rapidly deploy a cloud-managed Policy Server and virtual network sensor, an organization can quickly gain visibility to all IP-enabled devices connected to any network. Once this visibility is established, administrators can easily exempt all trusted devices from quarantine through the UI and enable a Default Deny / Zero Trust posture which blocks all new/unknown/untrusted devices and users from the network. This feature allows for Genian NAC to satisfy or supplement an organization’s existing Zero Trust initiative.
Best NAC Deployment Plan
Implementing Zero Trust
Vertical or Regional Market Limitation
Gartner Recommendation
“Focus on vendors that target organizations of your size and complexity and, in some instances, industry vertical or region. Because NAC is a mature market, many vendors are clearly aligned regarding SMB and large-enterprise opportunities or specialize in certain industry verticals and regions such as Europe and Southeast Asia.”
Genians Can
Genians has over 1,600 satisfied global customers across APAC, NA, LATAM and EMEA, including global Fortune 500 companies, the government, the military, energy, finance, healthcare, education, and more. Customers range in size and scope from over 200K endpoints deployed in a global enterprise network to SMB managing less than 100 endpoints in a flat network at the most affordable pricing with flexible deployment options.
Conclusion
Gartner “Market Guide for Network Access Control,” John Watts, et al, 12 May 2020 (Gartner subscription required)